Secure voice
Secure voice (alternatively secure speech or ciphony) is a term in cryptography for the encryption of voice communication over a range of communication types such as radio, telephone or IP. (Wikipedia).

Secure voice (alternatively secure speech or ciphony) is a term in cryptography for the encryption of voice communication over a range of communication types such as radio, telephone or IP. (Wikipedia).


Best secure and private email services review - guide to Gmail alternatives and encrypted email
Secure your privacy and claim a new encrypted email at these secure and private email services. Follow my guide to gmail alternatives and end-to-end encryption using private email providers as part of degoogleify campaign. I made this channel because I believe standing up against power an
From playlist TUTORIALS & HOW TO's

Signal - the most secure messenger for everyone
Signal Private Messenger is the most secure messaging app you can install on your phone. Support me through Patreon: https://www.patreon.com/thehatedone Join my channel and become a member to enjoy perks https://www.youtube.com/channel/UCjr2bPAyPV7t35MvcgT3W8Q/join - or donate anonymous
From playlist TUTORIALS & HOW TO's

Quick Look at Google Voice Apps for iOS
Apple recently approved several Google Voice apps on the App Store. We explain why that's rad.
From playlist Quick Looks

Quick Look at Google Voice Apps for iOS
Apple recently approved several Google Voice apps on the App Store. We explain why that's rad.
From playlist Quick Looks

VoIP Penetration Testing Lessons Learned 1/5
Speakers: - John Kindervag and Jason Ostrom clip 1/5
From playlist ShmooCon 2008

DEFCON 19: VoIP Hopping the Hotel: Attacking the Crown Jewels through VoIP
Speaker: Jason Ostrom Sipera VIPER Lab This presentation is about the security of VoIP deployed in hotel guest rooms. What it is, why it benefits administrators and users, and how easily it can be broken. The hospitality industry is widely deploying VoIP. Since 2008, we've seen an increas
From playlist DEFCON 19

DEFCON 13: End-to-End Voice Encryption over GSM: A Different Approach
Speakers: Wesley Tanner Nick Lane-Smith Where is end-to-end voice privacy over cellular? What efforts are underway to bring this necessity to the consumer? This discussion will distill for you the options available today, and focus on current research directions in technologies for th
From playlist DEFCON 13

DsiN Film Campaign for Secure Internet Use: Online Shopping
The film Secure Online Shopping shows how important it is to know who your business partners are and to only use secure payment options when shopping online. Source: Deutschland Sicher Im Netze (http://bit.ly/cRQoOo)
From playlist awareness

Speaker: Jan Seedorf Status Quo and Future Issues The presentation will give an overview on SIP security issues and show possible weaknesses in current implementations using SIP (Hardphones, Softphones, Gateways). Further, an outlook on the security of future, serverless SIP systems (P
From playlist 23C3: Who can you trust
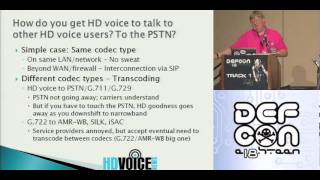
DEFCON 18: HD Voice: The Overdue Revolution 2/4
Speaker: Doug Mohney After kicking around on the back shelf for years, HD voice is finally gaining traction both in the broadband world and the cellular. And the French are leading the way! The audio standards for a POTS (Plain Old Telephone System) call have been frozen since about
From playlist DEFCON 18-2

VoIP Penetration Testing Lessons Learned 2/5
Speakers: - John Kindervag and Jason Ostrom clip 2/5
From playlist ShmooCon 2008

Introducing Twilio + IU REDCap
A 60-minute webinar about Creating Reports in IU REDCap. REDCap researchers now have more options to communicate using Twilio, a low-cost, third-party platform for communicating using SMS text messages and phone calls. Securely text survey links, alerts and notifications to research part
From playlist IU REDCap

DEFCON 16: VoIPER: Smashing the VoIP stack while you sleep
Speaker: N.N.P.Hacker, UnprotectedHex.com With VoIP devices finding their way into the majority of major enterprises and a significant number of residential installations, the possible consequences of a security vulnerability that can be leveraged by malicious hackers are ever increasing.
From playlist DEFCON 16

23C3: Mobile phone call encryption
Speakers: Paul Wouters, Leigh Honeywell Encrypting (GSM) mobile phone calls over VPN with an Asterisk PBX To encrypt all your mobile phones to protect it from overzealous eavesdroppers, you are currently limited to using special hardware such as the Cryptophone. The disadvantage of cr
From playlist 23C3: Who can you trust

VoIP Encryption in a Surveillance Society
March 7, 2007 lecture by Phillip Zimmermann for the Stanford University Computer Systems Colloquium (EE 380). Phil talks about how the debate on the use of crypto has shifted since the 1990s, when it was a clash between civil liberties and law enforcement - in the 1990s, the crypto debate
From playlist Course | Computer Systems Laboratory Colloquium (2006-2007)