Python 3 Programming Tutorial - Sys Module
This video covers some of the basics to the sys module in Python 3. The sys module allows you to use stdin() and stdout(), as well as stderr()... but, most interestingly, we can utilize sys.argv(). To many this is a confusing concept, but it is pretty simple and very useful once you learn
From playlist Python 3 Basics Tutorial Series

3 Derivatives of vector functions using SymPy
In this lecture I show you how easy it is to calculate the derivatives of a vector function using sympy.
From playlist Life Science Math: Vectors
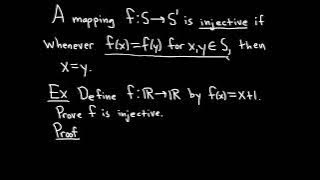
Definition of an Injective Function and Sample Proof
We define what it means for a function to be injective and do a simple proof where we show a specific function is injective. Injective functions are also called one-to-one functions. Useful Math Supplies https://amzn.to/3Y5TGcv My Recording Gear https://amzn.to/3BFvcxp (these are my affil
From playlist Injective, Surjective, and Bijective Functions

This video explains how to determine a unit vector given a vector. It also explains how to determine the component form of a vector in standard position that intersects the unit circle. http://mathispower4u.yolasite.com/
From playlist Vectors

Learning CentOS Linux Lesson 2 Upstart service configuration
More videos like this online at http://www.theurbanpenguin.com . CentOS 6.x introduces upstart to the Enterprise Linux range. Upstart is a new initialization deamon that was introduced by Ubuntu back in 1998. We are using CentOS 6.3 and since version 6 CentOS has been transitioning to upst
From playlist Learning Linux Centos

systemd on Linux 1: Intro and Unit Files
The first video in the systemd series, covering the basics of Linux init and systemd, including how to create systemd unit files for services. 0:00 Introduction 0:51 What is init in Linux? 1:45 SysV init 2:40 systemd's Components and Responsibilities 3:22 systemd Unit Types 4:52 Unit file
From playlist The Linux Basics Course: Beginner to Sysadmin, Step by Step
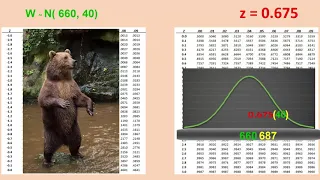
Determining values of a variable at a particular percentile in a normal distribution
From playlist Unit 2: Normal Distributions

Determine if the Given Value is from a Discrete or Continuous Data Set MyMathlab Statistics
Please Subscribe here, thank you!!! https://goo.gl/JQ8Nys Determine if the Given Value is from a Discrete or Continuous Data Set MyMathlab Statistics
From playlist Statistics

More Standard Deviation and Variance of Joint Discrete Random Variables
Further example and understanding of Joint Discrete random variables and their standard deviation and variance
From playlist Unit 6 Probability B: Random Variables & Binomial Probability & Counting Techniques

Installing Apache on Ubuntu 12 04 Server
More videos like this online at http://www.theurbanpenguin.com A quick install of Apache on Ubuntu. looking at how the services start and stop as this is still controlled through SySV scripts
From playlist Learning Ubuntu Server

RH124 CentOS 7 Managing services with systemd
More videos like this online at http://www.theurbanpenguin.com Red Hat Enterprise Linux 7 and the subscription free version CentOS 7 now use systemd over upstart and the earlier SysV scriots. Of course then you need to take a look at managing services with the new tools. We will install th
From playlist RH124
What Is Checksum Error Detection? | What Is Checksum And How It Works? | Simplilearn
"In this video on 'What Is Checksum?', we will look at one of the most applied error-detection methods of the network domain, the checksum method, along with details and the working steps of the checksum method. Topics covered in this video on 'What Is Checksum?' are as follows: 00:00:00
From playlist Networking
Checksums and Hamming distance
The term "checksum" can refer to all sorts of different error detection codes. How are some better than others? What types of errors are they good at detecting? And how do you calculate different types of checksums? Support these videos on Patreon: https://www.patreon.com/beneater or http
From playlist Error detection

26C3: Exposing Crypto Bugs through reverse engineering 4/5
Clip 4/5 Speaker: Philippe Oechslin Breaking good crypto is hard. It takes a genius to find a flaw in AES or Blowfish. On the other hand, it is also difficult to program cryptography correctly. Thus the simpler way of breaking a cryptographic software is often to reverse engineer it a
From playlist 26C3: Here be dragons day 1
Definition of a Surjective Function and a Function that is NOT Surjective
We define what it means for a function to be surjective and explain the intuition behind the definition. We then do an example where we show a function is not surjective. Surjective functions are also called onto functions. Useful Math Supplies https://amzn.to/3Y5TGcv My Recording Gear ht
From playlist Injective, Surjective, and Bijective Functions
Checksum is a method of checking for errors in a communications system. I'm Mr. Woo and my channel is all about learning - I love doing it, and I love helping others to do it too. I guess that's why I became a teacher! I hope you get something out of these videos - I upload almost every w
From playlist Communications & Network Systems

DEFCON 20: No More Hooks: Detection of Code Integrity Attacks
Speakers: XENO KOVAH THE MITRE CORPORATION COREY KALLENBERG THE MITRE CORPORATION Hooking is the act of redirecting program control flow somewhere other than it would go by default. For instance code can be "inlined hooked" by rewriting instructions to unconditionally transfer to other co
From playlist DEFCON 20
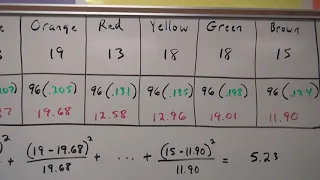
Chi Squared Goodness of Fit [GOF] on M and Ms Distribution
A classroom data-collecting activity on the distribution of M & M colors and performing and interpreting a Chi squared Goodness of Fit [GOF] test
From playlist Unit 10: Chi Squared

CS105: Introduction to Computers | 2021 | Lecture 20.2 Computer Security: Mechanisms
Patrick Young Computer Science, PhD This course is a survey of Internet technology and the basics of computer hardware. You will learn what computers are and how they work and gain practical experience in the development of websites and an introduction to programming. To follow along wi
From playlist Stanford CS105 - Introduction to Computers Full Course