
Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Stanford Seminar - Zero-Knowledge and the Next Digital Revolution
March 6, 2023 Alex Pruden of Aleo

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Ulterior States [IamSatoshi Documentary]
Ulterior States A Film By Tomer Kantor - An IamSatoshi Production Tip bitcoin: 1NkMgKPdwP63q5LFQW84dczJthFWYLwkoW http://www.iamsatoshi.com/ulterior-states-documentary Featuring (alphabetically): Andreas Antonopoulos Julian Assange Jessi Baker Adam Cleary Matt Corallo Sven Desai Kyle Dra
From playlist Interviews and Shows

Matt Debergalis and Emily Stark (Meteor) interviewed at Fluent 2014
Matt DeBergalis (Meteor), Emily Stark (Meteor Development Group)
From playlist Fluent Conference 2014

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

We don’t yet know what form it will take or when it will arrive, but the quantum computer is coming – and while its initial applications will be limited, they are likely to expand with time. Jonathan Home, Group Leader at ETH Zurich, discusses the current state of research and future possi
From playlist Quantum Computing

29C3: Re-igniting the Crypto Wars on the Web (EN)
Speaker: Harry Halpin This talk will give an overview of the ongoing work by the W3C on a controversial general purpose Javascript cryptography API in context of the larger desire to create trusted and encrypted cloud services with rich web applications. Today, cryptography is difficult t
From playlist 29C3: Not my department

Some Cryptographic Tools (in Blockchains) by Manoj Prabhakaran
DISCUSSION MEETING : FOUNDATIONAL ASPECTS OF BLOCKCHAIN TECHNOLOGY ORGANIZERS : Pandu Rangan Chandrasekaran DATE : 15 to 17 January 2020 VENUE : Madhava Lecture Hall, ICTS, Bangalore Blockchain technology is among one of the most influential disruptive technologies of the current decade.
From playlist Foundational Aspects of Blockchain Technology 2020

Introduction to Elliptic Curves 1 by Anupam Saikia
PROGRAM : ELLIPTIC CURVES AND THE SPECIAL VALUES OF L-FUNCTIONS (ONLINE) ORGANIZERS : Ashay Burungale (California Institute of Technology, USA), Haruzo Hida (University of California, Los Angeles, USA), Somnath Jha (IIT - Kanpur, India) and Ye Tian (Chinese Academy of Sciences, China) DA
From playlist Elliptic Curves and the Special Values of L-functions (ONLINE)
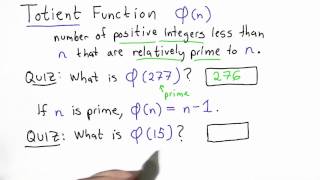
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Distributed Data Engineering for Science - OpSci - Holonym - DRT S2E16
02:10 Our favorite parts of brain 06:11 What does Shady (OpSci) do? 08:19 Shady's PhD work and the inspiration for a platform for data engineering for scientists 11:16 GitHub for complex datasets? 15:32 What's wrong with how scientific data sharing and handling works now and what can be d
From playlist Deep Random Talks- Season 2
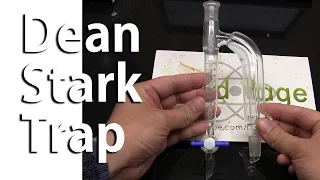
Lab Equipment: Dean Stark Trap
Glassware generously provided by http://www.alchemylabsupply.com/ Use the discount code "copper" for a 5% discount. Donate to NurdRage! Through Patreon (preferred): https://www.patreon.com/NurdRage Through Bitcoin: 1NurdRAge7PNR4ULrbrpcYvc9RC4LDp9pS In this video we construct and demonst
From playlist Lab Equipment

Lab Equipment: The Clevenger Apparatus
In this video we discuss the Clevenger Apparatus, a useful type of Dean-Stark apparatus that can be used in both light return and heavy return modes. Related Videos: The Dean Stark Apparatus: https://www.youtube.com/watch?v=jxgpLp279Yc Donate to NurdRage! Through Patreon (preferred): h
From playlist Lab Equipment

CryptoMathesis | Intro | What is Cryptography? | Caesar Cipher
Welcome to CryptoMathesis! This is a course to help you learn cryptography in depth with very simple explanation. In this video we will see what cryptography is, where we use it, and analyze Caesar Cipher! ############################################################# Καλώς ήλθατε στ
From playlist Summer of Math Exposition Youtube Videos