
Use point slope form to write the equation of a line given slope and point
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Writing an equation using point slope form given a point and slope
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Writing an equation using point slope form given a point and slope
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Writing an equation using point slope form given a point and slope
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Writing an equation using point slope form given a point and slope
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Using point slope form to find the equation of a line of a line given a point and slope
👉 Learn how to write the equation of a line in a point-slope form. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents in its variable(s)). There are various forms which we can write the equation of a line: the point-slope form, th
From playlist Write Linear Equations

Apply point slope form for two points to determine the slope and y intercept ex 4
👉 Learn how to write the equation of a line given two points on the line. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents on its variable(s)). There are various forms which we can write the equation of a line: the point-slope f
From playlist Write Linear Equations

25c3: Full-Disk-Encryption Crash-Course
Speaker: Juergen Pabel Everything to hide This is not a hacking presentation, no vulnerabilities are presented. It's a crash-course in full-disk-encryption ("FDE") concepts, products and implementation aspects. An overview of both commercial and open-source offerings for Windows, Linux,
From playlist 25C3: Nothing to hide

CERIAS Security: PrivacyEnhancing k-Anonymization of Customer Data 3/9
Clip 3/9 Speaker: Sheng Zhong · SUNY at Buffalo In order to protect individuals' privacy, the technique of k-anonymization has been proposed to de-associate sensitive attributes from the corresponding identifiers. In this work, we provide privacy-enhancing methods for creating k-anony
From playlist The CERIAS Security Seminars 2005 (2)

PDF is the most widely used standard for office documents. Supported by many desktop applications, email gateways and web services solutions, are used in all sectors, including government, business and private fields. For protecting sensitive information, PDFs can be encrypted and digitall
From playlist Security
Mathematics in Cryptography II - Toni Bluher
2018 Program for Women and Mathematics Topic: Mathematics in Cryptography II Speaker: Toni Bluher Affiliation: National Security Agency Date: May 21, 2018 For more videos, please visit http://video.ias.edu
From playlist Mathematics

Jonathan Katz - Introduction to Cryptography Part 1 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography I" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This lecture will serve as a "crash course" in modern cryptography for those with no prior exposure
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Privacy-Preserving Machine Learning with Fully Homomorphic Encryption
A Google TechTalk, presented by Jordan Fréry, 2023-01-17 ABSTRACT: In today's digital age, protecting privacy has become increasingly difficult. However, new developments such as Fully Homomorphic Encryption (FHE) provide a means of safeguarding sensitive client information. We are excite
From playlist Differential Privacy for ML

Digital security PART 2 - how to protect yourself on the Internet
Part 2 of the digital security talk with Daniel from Safing.io. In this part, we discuss specific tools and strategies you can use to enhance your security online. Support me through Patreon: https://www.patreon.com/thehatedone - or donate anonymously: Monero: 84DYxU8rPzQ88SxQqBF6VBNf
From playlist TUTORIALS & HOW TO's

SOURCE Boston 2009: Encryption and Enterprise Data Security
Speaker: Adrian Lane, Securosis We will follow the progression of data breaches and highlight some of the problems that most enterprises fail to address, and then examine uses of encryption to address issues of security within the context of business processing. •Why they fail: A look at
From playlist Latest uploads

RubyHack 2019 - A Better Way To Manage Secrets by Johnny T
RubyHack 2019 - A Better Way To Manage Secrets by Johnny T Do you know when your API keys are being used? Do you want to make compliance audits easier? Can you immediately stop rogue apps from decrypting sensitive data (during a data breach)? Come learn how to level up your app security a
From playlist RubyHack 2019
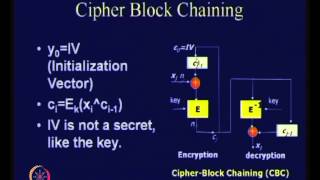
Modes of Operation of Block Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Writing an equation using point slope form given two points
👉 Learn how to write the equation of a line given two points on the line. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents on its variable(s)). There are various forms which we can write the equation of a line: the point-slope f
From playlist Write Linear Equations

Writing an equation using point slope form given two points
👉 Learn how to write the equation of a line given two points on the line. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents on its variable(s)). There are various forms which we can write the equation of a line: the point-slope f
From playlist Write Linear Equations

Writing an equation using point slope form given two points
👉 Learn how to write the equation of a line given two points on the line. The equation of a line is such that its highest exponent on its variable(s) is 1. (i.e. there are no exponents on its variable(s)). There are various forms which we can write the equation of a line: the point-slope f
From playlist Write Linear Equations