
What Is Quantum Computing | Quantum Computing Explained | Quantum Computer | #Shorts | Simplilearn
🔥Explore Our Free Courses With Completion Certificate by SkillUp: https://www.simplilearn.com/skillup-free-online-courses?utm_campaign=QuantumComputingShorts&utm_medium=ShortsDescription&utm_source=youtube Quantum computing is a branch of computing that focuses on developing computer tech
From playlist #Shorts | #Simplilearn

An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet

What Is Infrastructure As Code?
Infrastructure as code is a central idea in Continuous Delivery. The environment in which our software exists is a dependency of our software, so we need to control that environment as far as we can. If our aim is to release software reliably and repeatedly we need to control the variables
From playlist Software Engineering
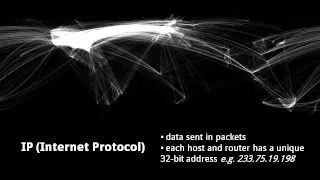
An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet

Open Source Quantum Computing: Write Your Own Quantum Programs
Quantum computers are not just science fiction anymore, with many companies building increasingly more powerful quantum computers. While, concepts in quantum computing have been around for over 30 years, but it hasn't been generally accessible until recently. Despite this quantum computing
From playlist Quantum Computing
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security

Source Boston 2010: Embedded System Hacking and My Plot to Take Over The World 5/5
Clip 5/5 Speaker: Paul Asadoorian, PaulDotCom It seems that as Moore's law is proven time and time again, we as a society are seeing more and more embedded systems help us in our daily lives. Embedded or purpose-built systems those that perform a specific function â are contained in the
From playlist SOURCE Boston 2010

Where the sex zombie parasites at? | Science on the Web #118
How do sex-boosting parasites work and why don't we see more of them in nature? Robert Lamb investigates… Subscribe | http://bit.ly/1AWgeM7 Homepage | http://bit.ly/stbym-hsw-home Listen to us | http://bit.ly/stbym-itunes Like us | http://bit.ly/stbym-fb Follow us | http://bit.ly/stbym-t
From playlist Animals!
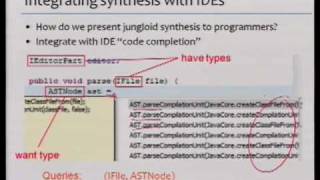
(October 9, 2009) Ras Bodik, from UC Berkeley Computer Science, discusses how partial programs can communicate programmer insight, how suitable synthesis algorithm completes the mechanics, and how end-user programming may be decomposable into partial program completion. Stanford Univers
From playlist Lecture Collection | Human-Computer Interaction Seminar (2009-2010)

Metapopulation dynamics and heterogeneity by Somdatta Sinha
Dynamics of Complex Systems - 2017 DATES: 10 May 2017 to 08 July 2017 VENUE: Madhava Lecture Hall, ICTS Bangalore This Summer Program on Dynamics of Complex Systems is second in the series. The theme for the program this year is Mathematical Biology. Over the past decades, the focus o
From playlist Dynamics of Complex Systems - 2017

Cuckoos and their victims: An evolutionary arms race
Cuckoos and their victims: An evolutionary arms race is 2015's Croonian Lecture by Professor Nicholas Davies FRS, given at the Royal Society, London, on Thursday 14 May 2015, 6.30-7.30pm BST. Nick Davies' fascinating lecture reveals one of nature's most interesting stories based on his ex
From playlist Popular talks and lectures

22C3: Syscall proxying fun and applications
Speaker: csk Introduction to syscall proxying and applications for in the wild exploitations This talk is about how using syscall proxying technique for envolved attacks or other distributed applications. It includes source code examples like shellcodes, tools and a poc rootkit using thi
From playlist 22C3: Private Investigations

A breakthrough unfolds - DeepMind: The Podcast (S2, Ep1)
In December 2019, DeepMind’s AI system, AlphaFold, solved a 50-year-old grand challenge in biology, known as the protein-folding problem. A headline in the journal Nature read, “It will change everything” and the President of the UK's Royal Society called it a “stunning advance [that arriv
From playlist DeepMind: The Podcast - Season 2

10/20/12 Richard Baxter - Of Men, Mosquitoes and Malaria
Richard Baxter - Of Men Mosquitoes and Malaria: Understanding Transmission of Global Disease Science on Saturdays is a special lecture series designed for families that brings the excitement of research and the passion of scientists to school-age children in the New Haven area. The lectur
From playlist Science on Saturday at Yale

The 4 Creepiest Parasites on Earth (This Will Keep You Up at Night!)
WARNING! This episode will freak you out. Did you know that almost half of all life on earth is parasitic? Join us for an eerie video hosted by Hank Green and learn about four of the creepiest parasites on Earth. Go to http://Brilliant.org/SciShow to try their Beautiful Geometry course.
From playlist Biology

Head to https://linode.com/scishow to get a $100 60-day credit on a new Linode account. Linode offers simple, affordable, and accessible Linux cloud solutions and services. In the fight against antibiotic-resistant bacteria, we might be able to find new treatments by looking at some of th
From playlist Uploads

Source Boston 2010: Embedded System Hacking and My Plot to Take Over The World 1/5
Clip 1/5 Speaker: Paul Asadoorian, PaulDotCom It seems that as Moore's law is proven time and time again, we as a society are seeing more and more embedded systems help us in our daily lives. Embedded or purpose-built systems those that perform a specific function â are contained in the
From playlist SOURCE Boston 2010


