
Few other Cryptanalytic Techniques
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
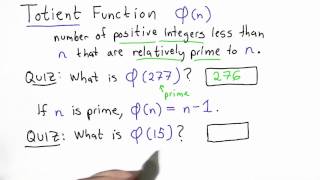
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
This video gives a general introduction to cryptography WITHOUT actually doing any math. Terms covered include cryptology vs cryptography vs cryptanalysis, symmetric vs public key systems, and "coding theory." NOTE: Yes, I said and wrote "cryptOanalysis" when it's actually "cryptanalysis
From playlist Cryptography and Coding Theory

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course

Overview on Modern Cryptography
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Black Hat USA 2010: WPA Migration Mode: WEP is Back to Haunt You 2/4
Speakers: Leandro Meiners, Diego Sor Cisco access points support WPA migration mode, which enables both WPA and WEP clients to associate to an access point using the same Service Set Identifier (SSID). If WEP clients are still around, we can use the traditional WEP cracking arsenal agains
From playlist BH USA 2010 - NETWORK

ShmooCon 2014: History of Bletchley Park and How They Invented Cryptography and the Computer Age
For more information visit: http://bit.ly/shmooc14 To download the video visit: http://bit.ly/shmooc14_down Playlist Shmoocon 2014: http://bit.ly/shmooc14_pl Speaker: Benjamin Gatti In the darkest days of WWII, a small team assembled at Bletchley Park solved two problems and set a new co
From playlist ShmooCon 2014

DEFCON 13: The Next Generation of Cryptanalytic Hardware
Speaker: The Next Generation of Cryptanalytic Hardware David Hulton, Dachb0den Labs Encryption is simply the act of obfuscating something to the point that it would take too much time or money for an attacker to recover it. Many algorithms have time after time failed due to Moore's law
From playlist DEFCON 13

Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security
ShmooCon 2014: The NSA: Capabilities and Countermeasures
For more information visit: http://bit.ly/shmooc14 To download the video visit: http://bit.ly/shmooc14_down Playlist Shmoocon 2014: http://bit.ly/shmooc14_pl Speaker: Bruce Schneier Edward Snowden has given us an unprecedented window into the NSA's surveillance activities. Drawing from b
From playlist ShmooCon 2014

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Black Hat USA 2010: WPA Migration Mode: WEP is Back to Haunt You 3/4
Speakers: Leandro Meiners, Diego Sor Cisco access points support WPA migration mode, which enables both WPA and WEP clients to associate to an access point using the same Service Set Identifier (SSID). If WEP clients are still around, we can use the traditional WEP cracking arsenal agains
From playlist BH USA 2010 - NETWORK
Stanford Seminar - Cryptology and Security: the view from 2016 - Whitfield Diffie
"Cryptology and Security: the view from 2016" - Whitfield Diffie, ACM 2015 Turing Award About the talk: On the face of it, the cryptographers have solved their piece of the puzzle but every other aspect of security, from crypto-implementations to operating systems to applications, stinks.
From playlist Engineering
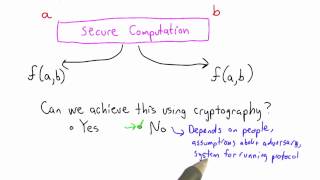
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

A Tutorial on Network Protocols
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
