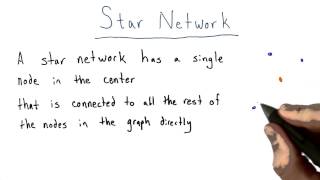
Star Network - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms
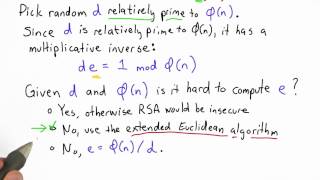
Compute E Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Euclidean Algorithm and Multiplicative Inverse (Ex. 1)
This video gives an example of how to use the Euclidean algorithm for finding a multiplicative inverse like this: x^-1 mod n = ?. For a second example: http://youtu.be/V2Ae-yEGq08 For using the algorithm to find gcd instead: http://youtu.be/WA4nP-iPYKE
From playlist Cryptography and Coding Theory
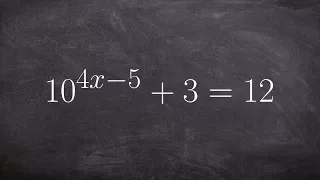
Use inverse operation to solve exponential equation without one to one property
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms

Lecture 12A : The Boltzmann Machine learning algorithm
Neural Networks for Machine Learning by Geoffrey Hinton [Coursera 2013] Lecture 12A : The Boltzmann Machine learning algorithm
From playlist Neural Networks for Machine Learning by Professor Geoffrey Hinton [Complete]
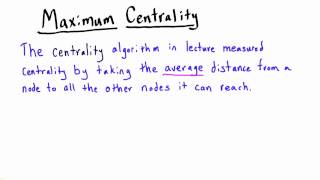
Centrality - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

Lecture 11 - Introduction to Neural Networks | Stanford CS229: Machine Learning (Autumn 2018)
For more information about Stanford’s Artificial Intelligence professional and graduate programs, visit: https://stanford.io/3nqNTNo Kian Katanforoosh Lecturer, Computer Science To follow along with the course schedule and syllabus, visit: http://cs229.stanford.edu/syllabus-autumn2018.
From playlist Stanford CS229: Machine Learning Full Course taught by Andrew Ng | Autumn 2018

Lions, Skunks, and Kangaroos: Geo-Distributed Learning on the Flickr-Mammal Dataset
A Google TechTalk, 2020/7/29, presented by Phillip Gibbons, Carnegie Mellon University ABSTRACT:
From playlist 2020 Google Workshop on Federated Learning and Analytics

R & Python - Entity Recognition Part 1 (2022)
Lecturer: Dr. Erin M. Buchanan Spring 2022 https://www.patreon.com/statisticsofdoom This video is part of my Natural Language Processing course. This video covers named entity recognition wherein you will learn about WordNET, training a spacy 2 pipeline, and how to extract entities from
From playlist Natural Language Processing

Explainable Neural Networks for Image and Text | by Konstantin Lopukhin | Kaggle Days Paris
Konstantin Lopukhin "Explainable neural networks for image and text" Kaggle Days Paris was held in January 2019 and gathered over 200 participants to meet, learn and code with Kaggle Grandmasters, and compete in our traditional offline competition. This edition is presented by LogicAI i
From playlist Kaggle Days Paris Edition | by LogicAI + Kaggle

Solving an exponential equation using the one to one property 16^x + 2 = 6
👉 Learn how to solve exponential equations. An exponential equation is an equation in which a variable occurs as an exponent. To solve an exponential equation, we isolate the exponential part of the equation. Then we take the log of both sides. Note that the base of the log should correspo
From playlist Solve Exponential Equations with Logarithms

Stitchcoding and Movie Color Maps
For the latest information, please visit: http://www.wolfram.com Speaker: Theo Gray and Nina Paley This talk discusses algorithmic stitchcoding, the process of creating pattern files for robotic quilting and embroidery machines, with unexpected results. It also covers how to turn an enti
From playlist Wolfram Technology Conference 2014

R & Python - Entity Recognition Part 1
Lecturer: Dr. Erin M. Buchanan Summer 2020 https://www.patreon.com/statisticsofdoom This video is part of my Natural Language Processing course. This video covers named entity recognition wherein you will learn about WordNET, training a spacy 2 pipeline, and how to extract entities from
From playlist Natural Language Processing

Simulate this Algorithm - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

From playlist CS50 Lectures 2013

CS50 2019 - Lecture 0 - Computational Thinking, Scratch
TABLE OF CONTENTS 00:00:00 - Introduction 00:02:35 - Representation 00:06:02 - Binary 00:09:17 - Binary Bulbs (Demo) 00:12:22 - Representing Letters 00:14:08 - Abstraction 00:15:35 - Unicode 00:17:21 - RGB 00:19:38 - Representing Images and Video 00:21:28 - Finding Mike Smith 00:24:54 - S
From playlist CS50 Lectures 2019

Running Time of Connected Component - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

Advanced 3. Image Classification via Deep Learning
MIT 16.412J Cognitive Robotics, Spring 2016 View the complete course: https://ocw.mit.edu/16-412JS16 Instructor: MIT students This is the fourth advanced lecture in 16.412 Cognitive Robotics of Spring 2016. Students presented the latest research of deep learning in image classification.
From playlist MIT 16.412J Cognitive Robotics, Spring 2016

Random Oracle - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
