
Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography
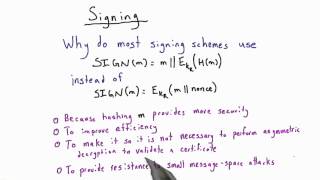
Signing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Certificates And Signatures Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

In this video I briefly go over the advantage to the Schnorr signature, and how to sign and verify.
From playlist Cryptography and Coding Theory
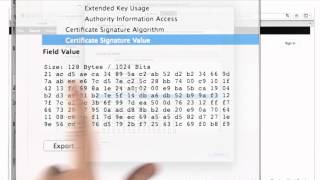
Certificates And Signatures - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography

Signature Validation - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Primality (1 of 2: Fermat's Test)
From playlist Cryptography

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live

Tech Talks 2020: New in Cryptography
Begins @ 2:52 Dariia Porechna talks about new elliptic curves, Schnorr digital signatures, PEM import and other improvements to cryptography functionality in Wolfram Language 12.2, as well as the upcoming Blockchain course on Wolfram U. Get started now with Wolfram|One: https://www.wolfra
From playlist Tech Talks: Wolfram Virtual Technology Conference 2020

WRI TwitchTalks Cryptography 101719
Presenter: Dariia Porechna Wolfram Research developers demonstrate the new features of Version 12 of the Wolfram Language that they were responsible for creating. Previously broadcast live on October 17, 2019 at twitch.tv/wolfram. For more information, visit: https://www.wolfram.com/langu
From playlist Twitch Talks

RSA and DSA Encryption Algorithms Explained | Cryptography & Network Security Tutorial | Simplilearn
In today's video on the RSA and DSA encryption algorithms explained, we cover the two most well known symmetric encryption algorithms in our cryptography & network security tutorial. We learn the steps needed to encrypt digital signatures and general data using RSA and DSA algorithms. The
From playlist Cyber Security Playlist [2023 Updated]🔥

In the modern world, cryptography is omnipresent. In this talk, Dariia Porechna will introduce recent and future developments to Wolfram Language cryptography functionality in the areas of digital signing and key and certificate management, as well as discussing efforts in teaching cryptog
From playlist Wolfram Technology Conference 2020

Cyber Security Interview Questions Part - 5 | Cryptography Interview Questions | Simplilearn
This video on cybersecurity interview questions part 5 focuses on questions from cryptography. This video will walk you through several questions related to encryption, decryption, public key infrastructure, and many more. 🔥Enroll for Free Cyber Security Course & Get Your Completion Certif
From playlist Cyber Security Playlist [2023 Updated]🔥

3. Blockchain Basics & Cryptography
MIT 15.S12 Blockchain and Money, Fall 2018 Instructor: Prof. Gary Gensler View the complete course: https://ocw.mit.edu/15-S12F18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP63UUkfL0onkxF6MYgVa04Fn In this lecture, Prof. Gensler, explains the basics of blockchain an
From playlist MIT 15.S12 Blockchain and Money, Fall 2018
I talk about the basics of the Key sharing algorithm in cryptography.
From playlist Cryptography
