Conversion Arcs and 2,916,485,648,612,232,232,816 (MegaFavNumbers)
I'm sorry. The MegaFavNumbers playlist: https://www.youtube.com/playlist?list=PLar4u0v66vIodqt3KSZPsYyuULD5meoAo
From playlist MegaFavNumbers

MegaFavNumbers: 1000001, my MegaFavNumber #MegaFavNumbers
To the haters: this can actually be represented by the formula ﷽ = 1 - |n| where n represents any number and ﷽ represents my personal level of joy and fulfillment (measured in "Coulombs".) Also, DON'T WORRY. The item seen at 0:35 is NOT any kind of w*apon. It's nothing but a regular railro
From playlist MegaFavNumbers

My entry in the #MegaFavNumbers project by James Grime and Matt Parker. The number in question is 2¹⁰²⁴, also known as 179,769,313,486,231,590,772,930,519,078,902,473,361,797,697,894,230,657,273,430,081,157,732,675,805,500,963,132,708,477,322,407,536,021,120,113,879,871,393,357,658,789,76
From playlist MegaFavNumbers

1,010,010,101,000,011 - #MegaFavNumbers
This is my submission to the #megafavnumbers project. My number is 1010010101000011, which is prime in bases 2, 3, 4, 5, 6 and 10. I've open-sourced my code: https://bitbucket.org/Bip901/multibase-primes Clarification: by "ignoring 1" I mean ignoring base 1, since this number cannot be fo
From playlist MegaFavNumbers

From playlist 708 hw 3

Metasploit For Beginners - #4 - Basic Exploitation
Hey, guys HackerSploit here, back again with another video. In this video, we will be continuing the Complete Metasploit Course, that will take you from a beginner to expert with Metasploit. The Metasploit Project is a computer security project that provides information about security vul
From playlist Ethical Hacking & Penetration Testing - Complete Course

This video was made for #MegaFavNumbers The sequence that is generated by cycles of bits and somehow related to prime numbers and multiplicative order of 2 mod 2n+1 Sequence: 3, 6, 15, 12, 255, 30, 63, 24, 315, 510, 33825, 60, 159783, 126, 255, 48, 65535, 630, 14942265, 1020, 4095, 67650
From playlist MegaFavNumbers

Kali Linux 2018.1 - Kernel Updates & Patches
Hey guys! HackerSploit here! Kali Linux has been updated to the 2018.1 release, what's new? Just a major kernel update! Kali Linux has over 600 preinstalled penetration-testing programs, including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a pack
From playlist Kali Linux

Kali Linux Quick Tips - #1 - Adding a non-root user
Hey guys! HackerSploit here back again with another video. Welcome to Kali Quickie, a series that aims to educate you on Kali Linux with tips, tricks, and guides. ---------------------------------------------------- HackerSploit Website: https://hsploit.com/ Pure VPN Affiliate Link: Pur
From playlist Kali Linux - Quick Tips

Shodan Search Engine Tutorial - Access Routers,Servers,Webcams + Install CLI
Shodan is a search engine that lets the user find specific types of computers (webcams, routers, servers, etc.) connected to the internet using a variety of filters. Some have also described it as a search engine of service banners, which are meta-data the server sends back to the client.
From playlist Ethical Hacking & Penetration Testing - Complete Course

Terminator - Kali Linux - Multiple Terminals
Kali Linux has over 600 pre-installed penetration-testing programs, including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a packet analyzer), John the Ripper password cracker, Aircrack-ng (a software suite for penetration-testing wireless LANs), B
From playlist Ethical Hacking & Penetration Testing - Complete Course
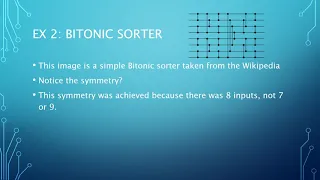
Why I love 4294967296? MegaFavNumbers.
Bitonic sorter: https://en.wikipedia.org/wiki/Bitonic_sorter Fast Fourier Transform https://en.wikipedia.org/wiki/Fast_Fourier_transform#:~:text=A%20fast%20Fourier%20transform%20(FFT,frequency%20domain%20and%20vice%20versa. #MegaFavNumbers I know that this video is horrible, but an invite
From playlist MegaFavNumbers

43,252,003,274,489,856,000 and 3,674,160 (#MegaFavNumbers)
#MegaFavNumbers If you have a favourite number over 1 million, post a video with you explaining why that number is so interesting.
From playlist MegaFavNumbers

Hey, guys HackerSploit here back again with another video, in this Q&A Video we will be looking at some interesting questions; 🔸What is port forwarding? 🔸Metasploitable 3 🔸My Thoughts on Mr Robot Channel Sponsor: PureVPN: https://billing.purevpn.com/aff.php?a... 📗 Get My Courses at $10
From playlist Q&A

MITM With Ettercap - ARP Poisoning
Hey guys! HackerSploit here back again with another video, in this video, we will be looking at how to perform a MITM with Ettercap. Ettercap is a comprehensive suite for man-in-the-middle attacks. It features sniffing of live connections, content filtering on the fly, and many other inter
From playlist Ethical Hacking & Penetration Testing - Complete Course

How To Setup And Use anonsurf On Kali Linux | Stay Anonymous
Anonsurf will anonymize the entire system under TOR using IPTables. It will also allow you to start and stop i2p as well. Und3rf10w forked ParrotSec’s git and made a version for Kali Linux which is very easy and straight forward to install. His repo contains the sources of both the anonsur
From playlist Ethical Hacking & Penetration Testing - Complete Course

Web Server Hacking - FTP Backdoor Command Execution With Metasploit - #2
Hey guys HackerSploit here back again with another video, in this video we will be hacking/gaining access to the Metasploitable web server! Exploit Link:https://www.rapid7.com/db/modules/exploit/unix/ftp/vsftpd_234_backdoor Metasploitable Link: https://sourceforge.net/projects/meta... 📗
From playlist Ethical Hacking & Penetration Testing - Complete Course

Q&A #1 - Best Cyber-security Certifications?
Hey, guys HackerSploit here back again with another video, in this Q&A Video we will be looking at some interesting questions; Best Cybersecurity certifications Best Hacking OS Best WIFI Adapter For Hacking Channel Sponsor: PureVPN: https://billing.purevpn.com/aff.php?aff=33288 📗 Get M
From playlist Q&A

#MegaFavNumbers - 7,588,043,387,109,376 by Egi
87,109,376^2=7,588,043,387,109,376. The last 8 digits is the square root😀, it's called an automorphic number which n^2 ends with n
From playlist MegaFavNumbers