Make A Combination Lock - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

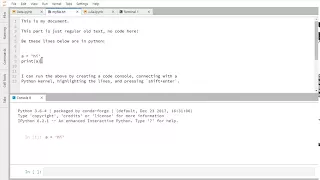
Demonstration of creating a text file using JupyterLab
From playlist JupyterLab Documentation

Demonstration of using the completer in a notebook using JupyterLab
From playlist JupyterLab Documentation
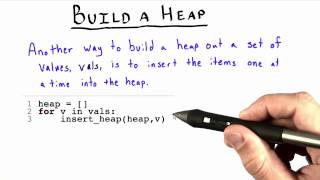
Build a Heap - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

JupyterLab text file creation with menu
Demonstration of creating a text file using the File menu.
From playlist JupyterLab Documentation

Jukebox: A Generative Model for Music (Paper Explained)
This generative model for music can make entire songs with remarkable quality and consistency. It can be conditioned on genre, artist, and even lyrics. Blog: https://openai.com/blog/jukebox/ Paper: https://cdn.openai.com/papers/jukebox.pdf Code: https://github.com/openai/jukebox/ Abstrac
From playlist Papers Explained

Graph regularity and counting lemmas - Jacob Fox
Conference on Graphs and Analysis Jacob Fox June 5, 2012 More videos on http://video.ias.edu
From playlist Mathematics

Pimp your brain: Sequenzanalyse
Die Abfolge der Basen A, C, G und T im Erbgut eines Lebewesens entscheidet über seine Eigenschaften. Wie die Fülle solcher Sequenzdaten aus der Molekularbiologie verarbeitet und interpretiert werden kann und ganz nebenbei auch eine Methode zur Plagiatsauffindung entstanden ist, erläutert d
From playlist Most popular videos

Lecture 1: Introduction to Data Structures and Algorithms - Richard Buckland
A selection of the course material is available at https://wiki.cse.unsw.edu.au/openlearning/computing2 This is the first lecture of COMP1927 Algorithms and Data Structures, which is the second computing course taken by first year computing students at UNSW. This course follows immediat
From playlist CS2: Data Structures and Algorithms - Richard Buckland

Data Science: Supervised vs. Unsupervised, Discrete vs. Continuous (00c)
Video Lecture from the course INST 414: Advanced Data Science at UMD's iSchool. Full course information here: http://www.umiacs.umd.edu/~jbg/teaching/INST_414/
From playlist Advanced Data Science

8 1 Randomized Selection Algorithm 22 min
From playlist Algorithms 1

Lecture 7: Data Structures and Algorithms - Richard Buckland
lecture 7 of comp 1927
From playlist CS2: Data Structures and Algorithms - Richard Buckland

JupyterLab keyboard shortcut editor
Demonstration of using the keyboard shortcut editor using JupyterLab
From playlist JupyterLab Documentation

CERIAS Security: Recent Attacks on MD5 3/6
Clip 3/6 Speaker: John Black · University of Colorado at Boulder Cryptology is typically defined as cryptography (the construction of cryptographic algorithms) and cryptanalysis (attacks on these algorithms). Both are important, but the latter is more fun. Cryptographic hash functions
From playlist The CERIAS Security Seminars 2006

Where is the 4th Ace in a Shuffled Deck? (part 1/2)
In this video we derive the exact probabilities of the 4th ace being the nth card of a shuffled deck. I'll supply the R code in the comments. Enjoy!
From playlist Summer of Math Exposition Youtube Videos

Demonstration of renaming a text file using JupyterLab.
From playlist JupyterLab Documentation

5 4 Choosing a Good Pivot 22min
From playlist Algorithms 1