
(ML 14.12) Viterbi algorithm (part 2)
The Viterbi algorithm (computing the MAP sequence of hidden states) for hidden Markov models (HMMs).
From playlist Machine Learning
The Viterbi Algorithm : Natural Language Processing
How to efficiently perform part of speech tagging! Part of Speech Tagging Video : https://www.youtube.com/watch?v=fv6Z3ZrAWuU Hidden Markov Model Video : https://www.youtube.com/watch?v=fX5bYmnHqqE My Patreon : https://www.patreon.com/user?u=49277905
From playlist Natural Language Processing

(ML 14.11) Viterbi algorithm (part 1)
The Viterbi algorithm (computing the MAP sequence of hidden states) for hidden Markov models (HMMs).
From playlist Machine Learning

Vigenere Cipher - Decryption (Known Key)
This video shows how to decrypt the ciphertext when the key is known. Decryption (unknown key): http://youtu.be/LaWp_Kq0cKs Encryption: http://youtu.be/izFivfLjD5E
From playlist Cryptography and Coding Theory

Lec 15 | MIT 6.451 Principles of Digital Communication II
Trellis Representations of Binary Linear Block Codes View the complete course: http://ocw.mit.edu/6-451S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.451 Principles of Digital Communication II

Data Science - Part XIII - Hidden Markov Models
For downloadable versions of these lectures, please go to the following link: http://www.slideshare.net/DerekKane/presentations https://github.com/DerekKane/YouTube-Tutorials This lecture provides an overview on Markov processes and Hidden Markov Models. We will start off by going throug
From playlist Data Science

Model based deep learning: Applications to imaging and communications - Yonina Eldar
Yonina Eldar - Weizmann Institute of Science Deep neural networks provide unprecedented performance gains in many real-world problems in signal and image processing. Despite these gains, the future development and practical deployment of deep networks are hindered by their black-box natur
From playlist Interpretability, safety, and security in AI

Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

From playlist CS50 Walkthroughs (Problem Sets)
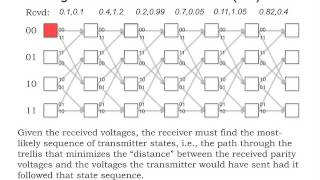
MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012 View the complete course: http://ocw.mit.edu/6-02F12 Instructor: George Verghese This lecture starts with a review of encoding and decoding. The Viterbi algorithm, which includes a branch netric and a path metric,
From playlist MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012

Lec 22 | MIT 6.451 Principles of Digital Communication II
Lattice and Trellis Codes View the complete course: http://ocw.mit.edu/6-451S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.451 Principles of Digital Communication II

Lec 24 | MIT 6.450 Principles of Digital Communications I, Fall 2006
Lecture 24: Case study — code division multiple access (CDMA) View the complete course at: http://ocw.mit.edu/6-450F06 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.450 Principles of Digital Communications, I Fall 2006

CMU Neural Nets for NLP 2017 (13): Parsing With Dynamic Programs
This lecture (by Graham Neubig) for CMU CS 11-747, Neural Networks for NLP (Fall 2017) covers: * What is Graph-based Parsing? * Minimum Spanning Tree Parsing * Structured Training and Other Improvements * Dynamic Programming Methods for Phrase Structure Parsing * Reranking Slides: http:/
From playlist CMU Neural Nets for NLP 2017
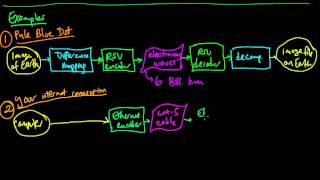
(IC 1.5) Examples of source-encoder-channel pipelines
Informal examples to illustrate the steps in the source-channel coding process. A playlist of these videos is available at: http://www.youtube.com/playlist?list=PLE125425EC837021F
From playlist Information theory and Coding
Solving an equation with parentheses
👉 Learn how to solve multi-step equations with parenthesis. An equation is a statement stating that two values are equal. A multi-step equation is an equation which can be solved by applying multiple steps of operations to get to the solution. To solve a multi-step equation with parenthes
From playlist How to Solve Multi Step Equations with Parenthesis
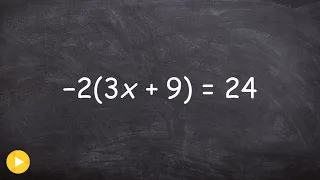
Solving an equation with parentheses
👉 Learn how to solve multi-step equations with parenthesis. An equation is a statement stating that two values are equal. A multi-step equation is an equation which can be solved by applying multiple steps of operations to get to the solution. To solve a multi-step equation with parenthes
From playlist How to Solve Multi Step Equations with Parenthesis

Solving an equation with parentheses
👉 Learn how to solve multi-step equations with parenthesis. An equation is a statement stating that two values are equal. A multi-step equation is an equation which can be solved by applying multiple steps of operations to get to the solution. To solve a multi-step equation with parenthes
From playlist How to Solve Multi Step Equations with Parenthesis

Lec 12 | MIT 6.451 Principles of Digital Communication II
Reed-Solomon Codes View the complete course: http://ocw.mit.edu/6-451S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.451 Principles of Digital Communication II

Vigenere Cipher - Decryption (Unknown Key)
This video shows the process (thoroughly) of how to find the key when you don't have it. English alphabet frequencies: http://www.math.cornell.edu/~mec/2003-2004/cryptography/subs/frequencies.html Decryption (known key): http://youtu.be/oHcJ4QLiiP8 Encryption: http://youtu.be/izFivfLjD5E
From playlist Cryptography and Coding Theory
