An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

Block Cipher Operation (BCO): Part 1
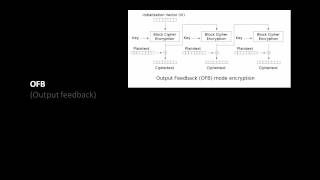
Fundamental concepts of Block Cipher Operation are discussed. Various extensions of DES are presented. Encryption modes for long messages are explained. Double DES, Triple DES, DES-X Encryption Modes for long messages: Electronic Code Book (ECB) Cipher Block Chaining (CBC) Cipher Feedback
From playlist Cryptography, Security

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain

Pseudorandom Number Generation and Stream Ciphers
Fundamental concepts of Pseudorandom Number Generation are discussed. Pseudorandom Number Generation using a Block Cipher is explained. Stream Cipher & RC4 are presented.
From playlist Network Security

Block Cipher Operation (BCO): Part 2
Fundamental concepts of Block Cipher Operation are discussed. Various extensions of DES are presented. Encryption modes for long messages are explained. Double DES, Triple DES, DES-X Encryption Modes for long messages: Electronic Code Book (ECB) Cipher Block Chaining (CBC) Cipher Feedback
From playlist Network Security

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

Raven vs. Mirage - Gulf War 1991
The incredible dogfight between an unarmed USAF EF-111 Raven and an Iraqi Mirage F.1 in January 1991. A fight with an unexpected outcome. Help support my channel: https://www.paypal.me/markfeltonproduction https://www.patreon.com/markfeltonproductions Disclaimer: All opinions and comment
From playlist Gulf War 1991

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Invasion of Iraq: How the British and Americans got it wrong
Strategy of the Iraq invasion by US and UK armies/politicians
From playlist History and Biographies
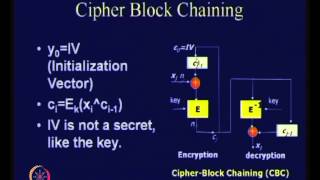
Modes of Operation of Block Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

The History of Cryptography: Block Cyphers, Stream Cyphers, Public Keys and more!
Alice and Bob have secrets they want to talk about without Eve being able to listen in. Worse yet, the mischievous Mallory delights in changing messages sent between parties. In such a hostile environment how can Alice talk to Bob without their messages being overheard and how can she be
From playlist Talks
Block Ciphers and Data Encryption Standard (DES) - Part 1
Fundamental concepts of Block Cipher Design Principles are discussed. DES is presented. Differential and linear cryptanalysis are explained . Block Cipher Principles Data Encryption Standard (DES) Differential and Linear Cryptanalysis Block Cipher Design Principles
From playlist Network Security

AES and DES Algorithm Explained | Difference between AES and DES | Network Security | Simplilearn
In today's video on AES and DES algorithm explained, we cover a major aspect of network security in encryption standards.The origins and working of both the data encryption standard and advanced encryption standard are covered. We also look into the applications and differences between AES
From playlist Cyber Security Playlist [2023 Updated]🔥

Modern Symmetric Ciphers - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography is a complex and confusing subject. In this talk you will learn about the core components of cryptography used in software development: securing data with encryption, ensuring data integrity with hashes and digital signatures, and protecting passwords with key derivation funct
From playlist Blockchain