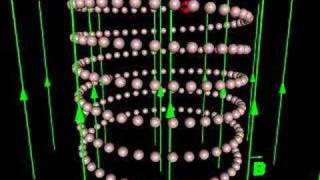
Charged particle in a magnetic field
Helicoidal motion of a charged particle in a uniform magnetic field. For other animations like this one, please visit http://web.ncf.ca/ch865
From playlist Magnetic Fields

EnCase Computer Forensics Demo
This is a short demo of EnCase I worked up. If you are interested in some of what professional computer forensics software can do then this is for you.
From playlist digital forensics

What to do with all those old PCBs from stuff you've taken apart...
From playlist Projects & Installations

The kinda creepy etymology of the most popular nickname for female breasts. Share this on Facebook: http://on.fb.me/1DNIp5n Share this on Twitter: http://ctt.ec/5U358 Subscribe: http://bit.ly/1l8JXv3 On the web: http://www.stuffmomnevertoldyou.com/ Twitter: https://twitter.com/momstuff
From playlist Word Stuff

More videos like this online at http://www.theurbanpenguin.com In this video we instal the bind (bind9) DNS software onto the Raspberry Pi and see how we can setup DNS on the little computer
From playlist Raspberry Pi

SYN Flood Denial of Service attack using perl script and hping3 tool.
From playlist Denial of Service attacks

Unpacking Princess Locker and Fixing Corrupted PE Header (OALabs x MalwareAnalysisForHedgehogs)
Open Analysis Live teams up with MalwareAnalysisForHedgehogs to unpack Princess Locker ransomware. We show how to use x64dbg and hooks on VirtualAlloc to dump the unpacked payload then fix the corrupted PE header... ----- OALABS DISCORD https://discord.gg/6h5Bh5AMDU OALABS PATREON https:
From playlist Open Analysis Live!

How To Unpack VMProtect 3 (x64) Night Sky Ransomware With VMPDump [Patreon Unlocked]
In this tutorial we unpack Night Sky Ransomware (x64) which is protected with VMProtect 3. We use VMPDump to dump and fix the imports and then re-create the virtualized entry point manually. No other functions are virtualized! Full tutorial on Patreon: https://www.patreon.com/posts/how-to
From playlist Patreon Unlocked

OverTheWire Bandit Walkthrough - Level 12
In this video i go through level 12 of the OverTheWire Bandit challenge. The objective of this level is to reverse a hex-dump and extract a file that has been repeatedly compressed with different compression utilities and formats. LINKS USED IN VIDEO: OverTheWire: https://overthewire.org
From playlist Linux

Assembly language vs. machine code — 6502 part 3
Schematics, datasheets, kits, and more at https://eater.net/6502 More on vasm: http://sun.hasenbraten.de/vasm Part 1: https://www.youtube.com/watch?v=LnzuMJLZRdU Part 2: https://www.youtube.com/watch?v=yl8vPW5hydQ Part 3: This video! Part 4: https://www.youtube.com/watch?v=FY3zTUaykVo Par
From playlist Build a 65c02-based computer from scratch

25c3: Repurposing the TI EZ430U
Speaker: Travis Goodspeed with msp430static, solder, and syringe USB devices are sometimes composed of little more than a microcontroller and a USB device controller. This lecture describes how to reprogram one such device, greatly expanding its potential. At only twenty dollars, the Te
From playlist 25C3: Nothing to hide

Unpacking VB6 Packers With IDA Pro and API Hooks (Re-Upload)
Open Analysis Live! We use the IDA Pro debugger and some API hooks to unpack a Visual Basic (VB6) packed sample and demonstrate a few tricks along the way. This is a re-uploaded classic from our old channel. Expand the description for more details... ----- OALABS DISCORD https://discord.g
From playlist Open Analysis Live!

Heap Sort - Intro to Algorithms
This video is part of an online course, Intro to Algorithms. Check out the course here: https://www.udacity.com/course/cs215.
From playlist Introduction to Algorithms

Unpacking Emotet / Geodo (Stage 1) Using x64dbg - Subscriber Request
Open Analysis Live! We use x64dbg to unpack a new Emotet / Geodo malware (Stage 1). This was a subscriber request asking us to determine how this was packed. ----- OALABS DISCORD https://discord.gg/6h5Bh5AMDU OALABS PATREON https://www.patreon.com/oalabs OALABS TIP JAR https://ko-fi.com
From playlist Open Analysis Live!

Buffer Overflows Made Easy - Part 6: Finding Bad Characters
https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers how to find the find bad characters in a buffer overflow process. We will examine the ESP dump and learn what bad characters look like, how they interact with shellcode, and their importance. Timestamps: 0:05 -
From playlist Buffer Overflows Made Easy

From playlist JS Bin tips & information

Process Memory Basics for Reverse Engineers - Tracking Memory With A Debugger [ Patreon Unlocked ]
Full Patreon tutorial (with examples): https://www.patreon.com/posts/process-memory-1-72454056 ----- OALABS DISCORD https://discord.gg/6h5Bh5AMDU OALABS PATREON https://www.patreon.com/oalabs Twitch https://www.twitch.tv/oalabslive OALABS GITHUB https://github.com/OALabs UNPACME - AU
From playlist Patreon Unlocked


