
Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography
An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography

From playlist Week 2 2015 Shorts

This video is a brief introduction to linear codes: dimensions, G (generating matrix), H (parity check matrix), their forms. Also gives an example of how to convert between G and H. Here is the formal definition of a Linear Code: A linear code of dimension k and length n over a field
From playlist Cryptography and Coding Theory

Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography
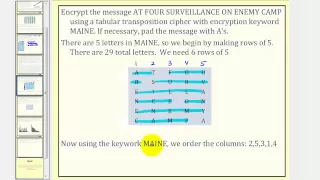
Cryptography: Transposition Cipher
This lesson explains how to encrypt and decrypt a message using a transposition cipher. Site: http://mathispower4u.com
From playlist Cryptography

Perfect Cipher - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Gravitational radiation from post-Newtonian sources.... by Luc Blanchet (Lecture - 3)
PROGRAM SUMMER SCHOOL ON GRAVITATIONAL WAVE ASTRONOMY ORGANIZERS : Parameswaran Ajith, K. G. Arun and Bala R. Iyer DATE : 15 July 2019 to 26 July 2019 VENUE : Madhava Lecture Hall, ICTS Bangalore This school is part of the annual ICTS summer schools on gravitational-wave (GW) astronomy.
From playlist Summer School on Gravitational Wave Astronomy -2019

Toy Substitution Cipher 2 Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Toy Substitution Cipher 1 - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Is Cryptocurrency Killing Us? (ft Jay Foreman) | The Big Question | Earth Lab
Jay Foreman (Unfinished London) looks at the how much energy is required to mine cryptocurrencies like Bitcoin, and what the future of money will look like. Watch more from Jay: https://www.youtube.com/user/jayforeman51 and follow him on twitter: @jayforeman Subscribe to Earth Lab for more
From playlist Earth Lab Originals - Fresh from the BBC Earth Lab

DEFCON 14: Secrets of the Hollywood Hacker!
Speaker: Johnny Long / j0hnny Abstract: Hacking stuff is for the birds. I'm taking a new path in life. I've decided to become a technical consultant for Hollywood. (No, not really, but work with me here). In my new role, I've decided it's time to take up the torch for all my fellow consul
From playlist DEFCON 14

Multiscale analysis of wave propagation in random media – Josselin Garnier – ICM2018
Probability and Statistics | Mathematics in Science and Technology Invited Lecture 12.6 | 17.6 Μultiscale analysis of wave propagation in random media Josselin Garnier Abstract: Wave propagation in random media can be studied by multiscale and stochastic analysis. We review some recent a
From playlist Mathematics in Science and Technology

Gambling, Computational Information, and Encryption Security - Bruce Kapron
Gambling, Computational Information, and Encryption Security Bruce Kapron University of Victoria; Member, School of Mathematics March 24, 2014 We revisit the question, originally posed by Yao (1982), of whether encryption security may be characterized using computational information. Yao p
From playlist Members Seminar

How To Teach Neural Networks To Read Handwriting With PyTorch & Keras | Session 03 | #AI
Don’t forget to subscribe! In this project series, you will learn how to teach the neural networks to read handwriting with PyTorch and Keras. We will use PyTorch and Keras tools to teach neural networks to read handwriting. Session 01: https://www.youtube.com/watch?v=SggGLRbYKoM&l
From playlist Teach Neural Networks To Read Handwriting With PyTorch & Keras

Sang-hyun Kim: Optimal regularity of mapping class group actions on the circle
Abstract: We prove that for each finite index subgroup H of the mapping class group of a closed hyperbolic surface, and for each real number r greater than 1 there does not exist a faithful C^r-action (in Hölder's sense) of H on a circle. For this, we partially determine the optimal regu
From playlist SMRI Algebra and Geometry Online

Item title reads - Biggest pudding. Australia donates a giant Christmas pudding to people of London. C/U as the giant pudding is carried into the Three Score Club. C/U sign: 'The Three Score Club'. M/S as pudding is put on table. C/U pudding. The Lord Mayor of London pours brandy o
From playlist Wartime Foods

GCSE Science Revision Chemistry "Alpha-Scattering Experiment"
Find my revision workbook here: https://www.freesciencelessons.co.uk/workbooks In this video, we look at the alpha-scattering experiment. First we look at an early model of atomic structure called the plum-pudding model. We then look at how scientists used the alpha-scattering experiment
From playlist 9-1 GCSE Chemistry Paper 1 Atomic Structure and the Periodic Table

Weak Ciphers - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
