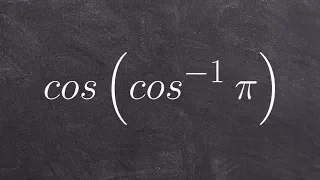
Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

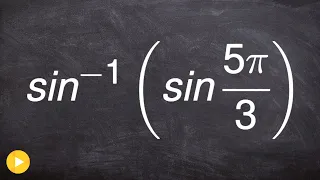
Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions
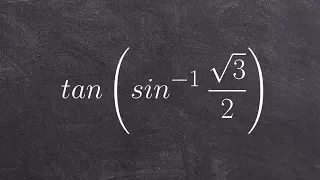
Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions
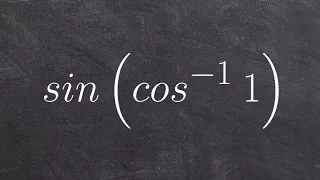
Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions
Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

Evaluating the composition of Functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

Evaluating the composition of inverse functions
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

White Hat vs Black Hat vs Grey Hat | Types Of Hackers Explained | #Shorts | Simplilearn
🔥FREE Ethical Hacking Course with Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=WhitehatvsBlackHatvsGreyHatShorts&utm_medium=DescriptionShorts&utm_source=youtube In this Simplilearn video on White Hat vs Black Hat vs Grey Hat we will
From playlist #Shorts | #Simplilearn

Cracking the Neural Code with Mathematica
Kai Gensel To learn more about the Wolfram Technologies, visit http://www.wolfram.com The European Wolfram Technology Conference featured both introductory and expert sessions on all major technologies and many applications made possible with Wolfram technology. Learn to achieve insight
From playlist European Wolfram Technology Conference 2015

Math Biology: Population Competition Model (Red vs Grey Squirrels)
TRM intern Amie Campbell explores the competitive exclusion population model and discusses how it can be applied to competition between species such as red and grey squirrels. Featuring differential equations, finding steady states, linear stability analysis, matrix eigenvalue calculatio
From playlist Mathstars
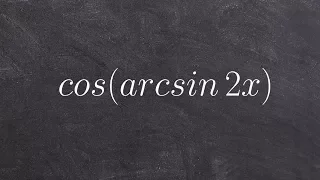
Composition of inverses using a triangle with variables
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

Dr. Aubrey de Grey and Dr. Rhonda Patrick Talk Aging
Dr. Aubrey de Grey is a biomedical gerontologist and the founder of the SENS research foundation which aims to find technologies that can repair the various types of damage that occur during the aging process. In this episode Rhonda and Aubrey discuss the types of damage that cause aging,
From playlist Interviews
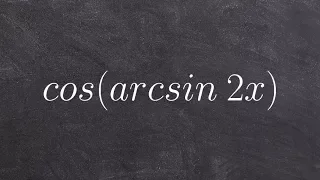
Evaluating the composition of inverse functions trigonometry
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

What Is Ethical Hacking? | Ethical Hacking Tutorial For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=WhatisEthicalHacking-gK73JLEbDs0&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecurity-b
From playlist Ethical Hacking Playlist [2023 Updated] 🔥

Squirrels, Turing and Excitability - Mathematical Modelling in Biology, Ecology and Medicine
The Grey Squirrel invasion explaining tumour cell proliferation? Alan Turing explaining football shirt patterns? The close relationship between slugs and the human heart? What is the common link? Mathematics of course. And Professor Philip Maini. Oxford Mathematics Public Lecture - Oxf
From playlist Oxford Mathematics Public Lectures

Lec 25 | MIT 7.012 Introduction to Biology, Fall 2004
Genomics (Prof. Eric Lander) View the complete course: http://ocw.mit.edu/7-012F04 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 7.012 Introduction to Biology, Fall 2004

Dawn Woodard: How Uber matches riders and drivers to reduce waiting time
Dynamic pricing, a key to the business model of Uber, depends on a complex algorithm that seeks equilibrium among a host of variables. If you use Uber to catch a ride now and then, you’ve probably noticed that a ride downtown at one time of day is a good deal cheaper (or more expensive) t
From playlist Women in Data Science Conference (WiDS) 2018
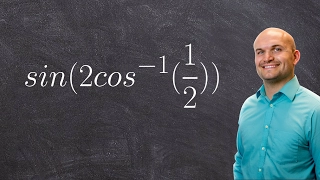
Learn how to evaluate the composition of a function and inverse function
👉 Learn how to evaluate an expression with the composition of a function and a function inverse. Just like every other mathematical operation, when given a composition of a trigonometric function and an inverse trigonometric function, you first evaluate the one inside the parenthesis. We
From playlist Evaluate a Composition of Inverse Trigonometric Functions

Ethical Hacker Full Course | Ethical Hacker Course For Beginners | Ethical Hacking | Simplilearn
🔥CEH v12 - Certified Ethical Hacking Course: https://www.simplilearn.com/cyber-security/ceh-certification?utm_campaign=EthicalHacking-6wKONaS1t2Q&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp (US Only): https://www.simplilearn.com/cybersecurity-bootcam
From playlist Simplilearn Live
