
Evaluate the left and right hand limit of basic ap calculus examples
👉 Learn about the limit of a function. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is said to exist if the value which the function approaches as x (or the inde
From playlist Evaluate the Limit..........Help!

Direct substitution with the left hand limit
👉 Learn how to evaluate the limit of a function involving rational expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct subst
From playlist Evaluate the Limit (PC)
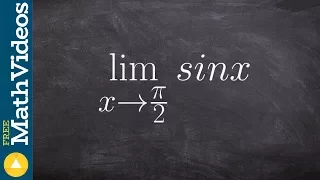
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

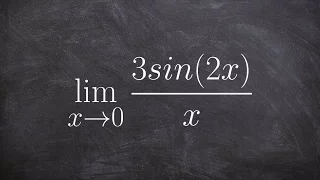
Using trig limits to evaluate the limit
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

[c][explained] Demystifying Pointers — Function Pointers
Find the complete program on https://www.notion.so/theteachr/Function-Pointers-9848de630cae47a7ad1ca5552d23a66d.
From playlist Demystifying Pointers

Use limit laws and special trig limits to evaluate
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

The IBM Quantum team will take you on an unprecedented technological deep dive into the future of quantum computing. Using our Development Roadmap as our guide, the team will be sharing many new technological breakthroughs from 2021, making more announcements for 2022, charting a course to
From playlist Quantum Computing
Learn how to use special trig limits to evaluate
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

Privacy-Aware Neural Network Classification & Training
From 25 June to 14 September 2018, 20 interns worked across nine projects. This series is a compilation of their final presentation. Speaker(s): Ali Shahin Shamsabadi, Queen Mary University of London Nitin Agrawal, University of Oxford We are currently involved in an exciting re-struct
From playlist Intern project presentations 2018

Evaluate the limit with tangent
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

SOURCE Boston 2008: Detailed Thread Modeling
Speakers: Nish Bhalla - Founder of Security Compass Krish Raja - Application Security Consultant with Security Compass Threat Modeling is quickly becoming a popular technique used to assess the security posture of an application's architectural components. But is there a way to perform su
From playlist SOURCE Boston 2008

Analog vs. Digital Epsilons: Implementation Considerations Considerations for Differential Privacy
A Google TechTalk, presented by Olya Ohrimenko, 2021/11/17 Differential Privacy for ML series.
From playlist Differential Privacy for ML

How to evaluate the special trig limit with sine and fractions
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig

Getting High-Quality Data for Your Computer Vision Models
Thought leaders in the Artificial Intelligence space such as Andrew Ng have been advocating for a shift from model-centric to data-centric AI. The idea behind this campaign is that AI models can be only marginally improved through tweaks in the algorithm but considerable change can only be
From playlist Fundamentals of Machine Learning

Unity - ECS (Entity, Component, System)
From playlist Unity game engine

O'Reilly Webcast: Developing Effective OCUnit and UI Automation Testing for iOS
The iPhone is a powerful development platform, but can be a difficult one to develop effective testing methodologies for. The OCUnit framework and the UIAutomation framework can allow developers to create unit tests with code coverage, and user interface level testing suites, but they can
From playlist O'Reilly Webcasts

Security Vulnerability Mitigations
Security vulnerabilities allow software to be manipulated in such a way that it misbehaves to the benefit of an attacker - security vulnerability mitigations work to thwart attempts to successfully exploit such a vulnerability. This landscape is continually changing in both the types of at
From playlist Security

Meltdown and Spectre - Professor Mark Handley, UCL
The Meltdown and Spectre vulnerabilities in almost all modern CPUs have received a great deal of publicity in the last week. Operating systems and hypervisors need significant changes to how memory management is performed, CPU firmware needs updating, compilers are being modified to avoid
From playlist Data science classes

Evaluate the trigonometric limit using limit laws
👉 Learn how to evaluate the limit of a function involving trigonometric expressions. The limit of a function as the input variable of the function tends to a number/value is the number/value which the function approaches at that time. The limit of a function is usually evaluated by direct
From playlist Evaluate Limits with Trig
