Can You Validate These Emails?
Email Validation is a procedure that verifies if an email address is deliverable and valid. Can you validate these emails?
From playlist Fun

Yes. I make mistakes ... rarely. http://www.flippingphysics.com
From playlist Miscellaneous

Can't edit signature in Outlook fix
Has your signature button disappeared in outlook? Tried to go into options to edit the signature but the buttons are all greyed out? This is how you fix it.
From playlist Technology

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

position:fixed juddering (real device)
Mirroring my phone to computer to record, you can see the same position:fixed juddering occurs in iOS 5.1.1
From playlist position:fixed

QED Prerequisites Geometric Algebra 17 - Bivector products
We examine Bivector-Bivector products using the canonical bivector form. Then we do a bit of bivector-bivector multiplication practice in the second half of the lesson, with a focus on the signature of the resulting product. Please consider supporting this channel on Patreon: https://www
From playlist QED- Prerequisite Topics

The Dynein Catch Bond: Implications for cooperative transport by Mithun Kumar Mitra
Collective Dynamics of-, on- and around Filaments in Living Cells: Motors, MAPs, TIPs and Tracks DATE: 28 October 2017 to 02 November 2017 VENUE: Ramanujan Lecture Hall, ICTS Bangalore Our knowledge of cytoskeletal filaments, nucleic acid filaments (DNA and RNA) as well as their associat
From playlist Collective Dynamics of-, on- and around Filaments in Living Cells: Motors, MAPs, TIPs and Tracks

Imprints of log-periodicity and the prediction to blowout in a turbulent .... by Ankan Banerjee
PROGRAM TIPPING POINTS IN COMPLEX SYSTEMS (HYBRID) ORGANIZERS: Partha Sharathi Dutta (IIT Ropar, India), Vishwesha Guttal (IISc, India), Mohit Kumar Jolly (IISc, India) and Sudipta Kumar Sinha (IIT Ropar, India) DATE: 19 September 2022 to 30 September 2022 VENUE: Ramanujan Lecture Hall an
From playlist TIPPING POINTS IN COMPLEX SYSTEMS (HYBRID, 2022)

Kernel Recipes 2016 - From ‘git tag’ to the front page - Konstantin Ryabitsev
Go on a detailed journey through the kernel.org infrastructure all the way from the moment Linus does “git tag” to when the front page of kernel.org says that there is a new kernel release available. Konstantin Ryabitsev, Linux Foundation
From playlist Kernel Recipes 2016

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Black Hat USA 2010: TitanMist: Your First Step to Reversing Nirvana 5/5
Speakers: Mario Vuksan, Tomislav Pericin Security is notoriously disunited. Every year multiple tools and projects are released and never maintained. TitanMist is its inverse opposite. Built on top of TitanEngine, it provides automation and manages all known and good PEID signatures, unpa
From playlist REVERSE ENGINEERING REDUX

CERIAS Security: Vulnerability-Driven Network Filters for Preventing Known Vulnerability Attacks 4/6
Clip 4/6 Speaker: Helen J. Wang · Microsoft Research Software patching has not been an effective first-line defense preventing large-scale worm attacks, even when patches had long been available for their corresponding vulnerabilities. Generally, people have been reluctant to patch th
From playlist The CERIAS Security Seminars 2005 (2)

Malware Software Armoring Circumvention 3/5
Speaker: Danny Quist clip 3°5
From playlist ShmooCon 2008

DeepSec 2010: OsmocomBB: A tool for GSM protocol level security analysis of GSM networks
Thanks to the DeepSec organisation for making these videos available and let me share the videos on YouTube. Speaker: Harald Welte, hmw-consulting The OsmocomBB project is a Free Software implementation of the GSM protocol stack running on a mobile phone. For decades, the cellular indust
From playlist DeepSec 2010

How do Naval Mines Work? | Unclassified Documentary | A Closer Look
This video is an original documentary produced by Concerning Reality. Timecodes for each section: History of Mines: 1:36 The Anatomy of a Mine: 6:25 Types of Mines: 8:25 Ways to Deploy a Mine: 9:48 Mine Actuation: 12:02 Destructive Power: 14:45 Credits: 16:44 Naval mines have been used
From playlist Concerning Questions

Sennheiser HD 558 Open-Back Headphones Review!
Let's take a look at the Sennheiser HD 558's -- a pair of serious high-end headphones that anyone can enjoy. Sennheiser HD 558 product page: http://en-us.sennheiser.com/audio-headphones-high-end-hd-558 ----------------------------------------------------------------------------- Please
From playlist Headphones & Personal Audio

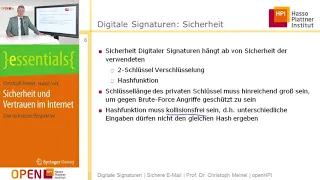
Fundamental concepts of Digital Signatures are discussed. ElGamal and Schnorr Digital Signature schemes are analyzed. Digital signature standard is presented.
From playlist Network Security