
Primality (1 of 2: Fermat's Test)
From playlist Cryptography
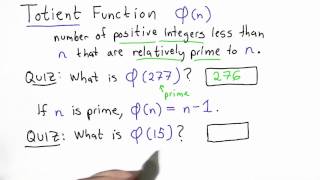
Totient Function - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
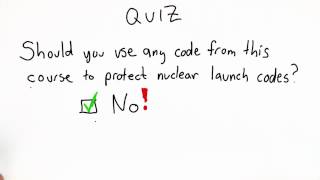
Do Not Implement Your Own Crypto Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
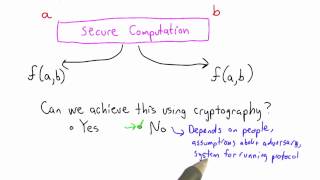
Secure Computation Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Timing Side Channel - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DEFCON 19: We're (The Government) Here To Help: A Look At How FIPS 140 Helps (And Hurts) Security
Speaker: Joey Maresca Many standards, especially those provided by the government, are often viewed as more trouble the actual help. The goal of this talk is to shed a new light onto onesuch standard (FIPS 140) and show what it is inteded for and how is can sometimes help ensure good desi
From playlist DEFCON 19
Side Channel Analysis of Cryptographic Implementations
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Totient - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

A brief description of the "Basic Principle" and how it can be used to test for primality.
From playlist Cryptography and Coding Theory

NIST - Missions and impacts to US industry, economy and citizens - James St. Pierre, Matthew Scholl
NIST - Missions and impacts to US industry, economy and citizens - James St. Pierre, Matthew Scholl Founded in 1901 and now part of the U.S. Department of Commerce, NIST is one of the nation's oldest physical science laboratories. Congress established the agency to remove a major handicap
From playlist AppSecUSA 2013

Cryptanalysis of Classical Ciphers
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Quantum Verification - Bourbaphy - 17/11/18
Elham Kashefi (CNRS LIP6) / 17.11.2018 Quantum Verification ---------------------------------- Vous pouvez nous rejoindre sur les réseaux sociaux pour suivre nos actualités. Facebook : https://www.facebook.com/InstitutHenriPoincare/ Twitter : https://twitter.com/InHenriPoincare Instagr
From playlist Bourbaphy - 17/11/18 - L'information

NOTACON 5: Current Election Technologies and How to Improve
Speakers: Smoke and Phreak This presentation will cover the current voting technologies from touch screens to optical scanners. We will also be covering the future of electronic election technologies, focusing on more securable software and hardware cryptographic protocols such as the Tru
From playlist Notacon 5

GRCon21 - Rampart Communications: Cryptographic Modulation: Zero-Attack-Surface Wireless
Presented by Keith Palmisano at GNU Radio Conference 2021 Wireless communication is the fabric of modern connectivity, but no one thinks of wireless as inherently secure. Fundamentally, it’s a means of easily increasing access and mobility, but as much as we want high-speed no-drop 5G/wif
From playlist GRCon 2021

23C3: Building an Open Source PKI using OpenXPKI
Speakers: Alexander Klink,Michael Bell Take a lot of Perl, add some OpenSSL, sprinkle it with a few HSMs, stir, season to taste, enjoy! OpenXPKI is an open source trust center software, written by the OpenXPKI Project, which aims to create an enterprise-scale PKI solution. You can see
From playlist 23C3: Who can you trust

DEFCON 13: End-to-End Voice Encryption over GSM: A Different Approach
Speakers: Wesley Tanner Nick Lane-Smith Where is end-to-end voice privacy over cellular? What efforts are underway to bring this necessity to the consumer? This discussion will distill for you the options available today, and focus on current research directions in technologies for th
From playlist DEFCON 13

Data-driven materials discovery | The Royal Society
Join us for the Clifford Paterson Lecture 2020 given by Professor Jacqui Cole. #crystallography #chemistry #energy #materials #ai Join the discussion: https://app.sli.do/event/ovdxfNLv5bS1gHViyN9P14 StreamText offers a full page of captions and you can personalise the display adjusting
From playlist Latest talks and lectures

Challenge Question - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

DEFCON 20: Embedded Device Firmware Vulnerability Hunting Using FRAK
Speaker: ANG CUI RED BALLOON SECURITY We present FRAK, the firmware reverse analysis konsole. FRAK is a framework for unpacking, analyzing, modifying and repacking the firmware images of proprietary embedded devices. The FRAK framework provides a programmatic environment for the analysis
From playlist DEFCON 20

Modular Exponentiation Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography