Definition of a Critical Number with Examples
Please Subscribe here, thank you!!! https://goo.gl/JQ8Nys Definition of a Critical Number with Examples
From playlist Calculus 1 Exam 2 Playlist

Critical Values of Functions (1 of 2: Insights produced by Critical Values)
More resources available at www.misterwootube.com
From playlist Further Work with Functions (related content)

Definition of critical numbers and two examples of how to find critical numbers for a polynomial and a rational function.
From playlist Calculus

Find the critical values of an absolute value function
👉 Learn how to find the critical values of a function. The critical values of a function are the points where the graph turns. They are also called the turning points of a function. To obtain the critical points of a function, first, we obtain the first derivative of the function. Next, w
From playlist Find the Critical Values of a Function

Learn how to find the critical values of a function
👉 Learn how to find the critical values of a function. The critical values of a function are the points where the graph turns. They are also called the turning points of a function. To obtain the critical points of a function, first, we obtain the first derivative of the function. Next, w
From playlist Find the Critical Values of a Function

How To Find CRITICAL Numbers In Calculus!! #Math #Graphs #Calculus #College #NicholasGKK #Shorts
From playlist Calculus

OWASP AppSecUSA 2011: Secure Programming Support in IDE
Speakers: Dr. Bill Chu, Jing Xie Many of today's application security vulnerabilities are introduced by software developers writing insecure code. The OWASP community has already reached a consensus that developers do not write secure code for all kinds of reasons. We believe a lack of un
From playlist OWASP AppSecUSA 2011

How to find + classify critical points of functions
Download the free PDF http://tinyurl.com/EngMathYT This video shows how to calculate and classify the critical points of functions of two variables. The ideas involve first and second order derivatives and are seen in university mathematics.
From playlist Several Variable Calculus / Vector Calculus

DeepSec 2007: Attacking the Giants: Exploiting SAP Internals
Thanks to the DeepSec organisation for making these videos available and let me share the videos on YouTube. Speaker: Mariano Nuñez Di Croce, CYBSEC The SAP Remote Function Call (RFC) Interface is the heart of communications between SAP systems, and between SAP and external software. Alm
From playlist DeepSec 2007

FUT1436 SUSE Linux Enterprise Mission Critical Simple Can Be Powerful
This future session was delivered at SUSECON in April 2019, in Nashville, TN. Abstract: SUSE Linux Enterprise Mission Critical is made up from SUSE Linux Enterprise, SUSE Linux Enterprise High Availability and SUSE Linux Enterprise Live Patching. Learn how SUSE have developed s olutions po
From playlist SUSECON 2019

DEFCON 19: Hacking and Forensicating an Oracle Database Server
Speaker: David Litchfield David Litchfield is recognized as one of the world's leading authorities on database security. He is the author of Oracle Forensics, the Oracle Hacker's Handbook, the Database Hacker's Handbook and SQL Server Security and is the co-author of the Shellcoder's Hand
From playlist DEFCON 19

Learn how to find the critical values of a polynomial
👉 Learn how to find the critical values of a function. The critical values of a function are the points where the graph turns. They are also called the turning points of a function. To obtain the critical points of a function, first, we obtain the first derivative of the function. Next, w
From playlist Find the Critical Values of a Function

RPA Blue Prism Full Course | Blue Prism Tutorial For Beginners | Blue Prism Tutorial | Simplilearn
This Blue Prism full course will help you understand what is Blue Prism, how to install Blue Prism, Blue Prism tutorial along with most important Blue Prism interview questions. 🔥Enroll for Free RPA Course & Get Your Completion Certificate: https://www.simplilearn.com/learn-rpa-basics-skil
From playlist Simplilearn Live

OWASP AppSec EU 2013: OWASP Top 10 Proactive Controls
For more information and to download the video visit: http://bit.ly/appseceu13 Playlist OWASP AppSec EU 2013: http://bit.ly/plappseceu13 Speaker: Jim Manico The major cause of web insecurity is poor development practices. We cannot "firewall" or "patch" our way to secure websites. Progra
From playlist OWASP AppSec EU 2013

CGSR | Russia’s AI Innovation Trajectory An Uncertain Future
Abstract: While Russia lags behind the United States and China in artificial intelligence development and integration, in both commercial and military applications, the Russian leadership has identified AI as a strategic technology, directing resources to shore up AI research, improve data
From playlist Center for Global Security Research

CISA Certification Training By Simplilearn | Live Virtual Class
Simplilearn’s CISA certification training is aligned to ISACA and ensures that you ace the exam in your first attempt. The training will enhance your understanding of IS audit processes and also help you understand how to protect information systems. 🔥Free CISA Course: https://www.simplile
From playlist CISA Training Videos

Discovering Hidden Properties to Attack NodeJS Ecosystem
Node.js is widely used for developing both server-side and desktop applications. It provides a cross-platform execution environment for JavaScript programs. Due to the increasing popularity, the security of Node.js is critical to web servers and desktop clients. We present a novel attack
From playlist Security

Yury Stepanyants: The asymptotic approach for ocean wave patterns
SMRI Applied Mathematics Seminar: Yury Stepanyants (University of Southern Queensland) Abstract: The asymptotic approach is suggested for the description of interacting surface and internal oceanic solitary waves. This approach allows one to describe a stationary moving wave patterns cons
From playlist SMRI Seminars
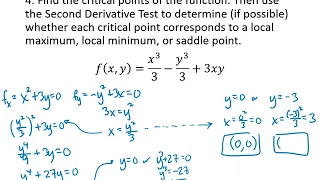
Multivariable Maximum and Minimum Problems
In this video, we will work through several examples of problems where we find critical points of multivariable functions and test them to find local maximum and local minimum points.
From playlist Multivariable Calculus
