
If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Cover Letters

Cover letter tips: Write the perfect cover letter for your job application.
When it comes to job hunting, getting your cover letter right is just as important as perfecting your CV. After all, your cover letter is a platform to introduce yourself to the employer and is sent to accompany and expand upon your CV. We know that writing these letters can seem daunti
From playlist Cover Letters

In this video, you’ll learn about HTML and how it is used to code webpages. We hope you enjoy! To learn more, check out our Basic HTML tutorial here: https://edu.gcfglobal.org/en/basic-html/ #whatishtml #htmlcode #learnhtml
From playlist HTML

An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet

Tips for job seekers: How to write a great cover letter pt. 2
Start your job search today: http://cb.com/TcB1VY Cover letters should be specific to the position you are applying to and what makes you stand out from other candidates, not just a reiteration of what's already on your resume. Always get to the point and convey your personality through w
From playlist Cover Letters

Constructing an Unbeatable Cover Letter: Introduction
Your cover letter is the first communication you make with a potential employer. It's your first impression, and the only one you've got, so it better be a good one. Here's how to get it off to the right start.
From playlist Cover Letters

Tips for Creating a Great Cover Letter
In this video, you’ll learn more about how to create a strong cover letter that recruiters and hiring managers will notice. Visit https://www.gcflearnfree.org/coverletters/crafting-your-cover-letter/1/ to learn even more. We hope you enjoy!
From playlist Searching for a Job

Network Security, Part 1 : Basic Encryption Techniques
Fundamental concepts of network security are discussed. It provides a good overview of secret Key and public key Encryption. Important data encryption standards are presented.
From playlist Network Security

If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Graphic Design

Ivelisse Rubio: "Exploring, generalizing and applying the covering method"
Latinx in the Mathematical Sciences Conference 2018 "Exploring, generalizing and applying the covering method" Ivelisse Rubio, University of Puerto Rico, Rio Piedras ABSTRACT: The divisibility of exponential sums has been used to characterize and prove properties in coding theory, crypto
From playlist Latinx in the Mathematical Sciences 2018

Best Books For Coding | Best Book To Learn Coding For Beginners | Learn Coding | Simplilearn
This video on Top Coding Books covers the Best Books for Coding in the professional world. The main aspect of the video is to deliver the best book to learn coding for beginners. It covers all beginner, intermediate and advanced level coding books. 00:00:00 Automating Boring Stuff with Py
From playlist C++ Tutorial Videos

Wicked Good Ruby 2013 - Outside-In Testing by Nick Gauthier
As a freelancer I'm often tasked with creating high quality web applications quickly while keeping the budget razor thin. In my experience, the absolute best bang-for-your-buck style of development has been BDD from the outside-in via acceptance tests. With acceptance tests you can quickly
From playlist Wicked Good Ruby 2013

An Introduction to Programming
Welcome to An Introduction to Programming. In this lecture-style series, we will be taking you through the basics of computer science and giving you the tools required to delve into any programming language you would like to learn. This video hopes to give you a good base onto which you ca
From playlist Software Development

Introduction to Programming and Computer Science - Full Course
In this course, you will learn basics of computer programming and computer science. The concepts you learn apply to any and all programming languages and will be a good base onto which you can build your skills. This video is meant for those who are interested in computer science and pro
From playlist Computer Science Concepts

Maria Montanucci: Algebraic curves with many rational points over finite fields
CONFERENCE Recording during the thematic meeting : « Conference On alGebraic varieties over fiNite fields and Algebraic geometry Codes» the February 13, 2023 at the Centre International de Rencontres Mathématiques (Marseille, France) Filmmaker: Jean Petit Find this video and other talks
From playlist Algebraic and Complex Geometry
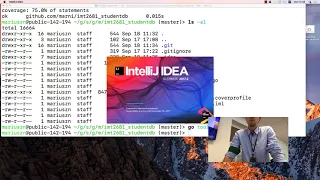
Go programming: debugging, testing and test coverage. Discussion.
IMT2681, Cloud Computing, Lecture/Review. Monday session. Discussion on testing, submission, debugging, code coverage.
From playlist Archive - Cloud Computing

Top 5 Coding Books For 2023 | Best Coding Books For Beginners | Learn Coding | Simplilearn
🔥 Caltech Coding Bootcamp By Simplilearn (US Only): https://www.simplilearn.com/coding-bootcamp?utm_campaign=Top5CodingBooks-2DgwIfUBAeM&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥 Post Graduate Program In Full Stack Web Development: https://www.simplilearn.com/pgp-full-stack-web-
From playlist Top 10 Trending Videos 2023

Kernel Recipes 2018 - A year of fixing Coverity issues... - Gustavo A. R. Silva
Coverity is a static analyzer that scans the kernel code and reports issues that can hide coding mistakes and vulnerabilities. Currently, it reports around 5,000 outstanding defects in the Linux kernel. I’m dedicated to fixing those defects and, this talk is a status report of the work I h
From playlist Kernel Recipes 2018

An Introduction to Binary Code Bounds - Fernando Granha Jeronimo
A binary code is simply any subset of 0/1 strings of a fixed length. Given two strings, a standard way of defining their distance is by counting the number of positions in which they disagree. Roughly speaking, if elements of a code are sufficiently far apart, then the code is resilient to
From playlist Mathematics

The Recipe for a Perfect Cover Letter
--- Subscribe to Monster on YouTube: https://www.youtube.com/monster Need to find a job? Become a Monster member today: https://member.monster.com/?WT.mc_n=SM_PR_YT Want career tips and guidance? Visit our advice site: http://career-advice.monster.com/?WT.mc_n=SM_PR_YT Looking to post
From playlist Cover Letters