
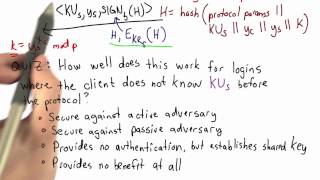
EKE Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Convincing Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Signature Validation - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Handshake Recap - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
SSH Authentication - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Public Key Cryptography: Diffie-Hellman Key Exchange (short version)
This is a segment of this full video: https://www.youtube.com/watch?v=YEBfamv-_do Diffie-Hellman key exchange was one of the earliest practical implementations of key exchange within the field of cryptography. It relies on the discrete logarithm problem. This test clip will be part of the
From playlist Cryptography, Security

Certificates - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

How To Build A Decentralized Crypto Exchange Operating On Ethereum | Introduction | #ethereum
Don’t forget to subscribe! In this project series, we are going to build a decentralized crypto exchange, a website where we can deposit ether and tokens. You will learn how to withdraw tokens and also to develop, sell and buy orders, where we can trade the tokens for a price. A crypto e
From playlist Build A Decentralized Crypto Exchange

Lec 23 | MIT 6.033 Computer System Engineering, Spring 2005
Authorization and Confidentiality View the complete course at: http://ocw.mit.edu/6-033S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.033 Computer System Engineering, Spring 2005

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live

Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=CryptographyFCAug17&utm_medium=DescriptionFirstFold&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity
From playlist Simplilearn Live

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
OpenSSH Internals for PowerShell Pros by Anthony Nocentino In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd config
From playlist PowerShell + DevOps Global Summit 2018

OpenSSH Internals for PowerShell Pros by Anthony Nocentino
In PowerShell Core we can use OpenSSH as the transport layer to carry our remoting sessions between our systems. In this session we’ll look at OpenSSH architecture, Authentication methods, including key authentication, sshd configuration, and troubleshooting methods when things go wrong!
From playlist PowerShell + DevOps Global Summit 2018

Source Boston 2010: Changing Threats To Privacy: From TIA to Google 5/6
Clip 5/6 Speaker: Moxie Marlinspike A lot has changed since discussions around digital privacy began. The security community won the war for strong cryptography, anonymous darknets which presumably make the eradication of information impossible have been successfully deployed, and much of
From playlist SOURCE Boston 2010

🔥Cryptography And Network Security Full Course 2022 | Cryptography | Network Security | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CryptographyNetworkSecurityFC4Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on the Cryptography and network security full course will
From playlist Simplilearn Live

Blackhat Europe 2010: Changing Threats To Privacy: From TIA to Google 5/7
Clip 5/7 Speaker: Moxie Marlinspike We won the war for strong cryptography, anonymous darknets exist in the wild today, and decentralized communication networks have emerged to become reality. These strategies for communicating online were conceived of in anticipation of a dystopian futur
From playlist Black Hat Europe 2010

DEFCON 18: Changing Threats To Privacy: From TIA to Google 3/3
Speaker: Moxie Marlinspike A lot has changed since discussions around digital privacy began. The security community won the war for strong cryptography, anonymous darknets have been successfully deployed, and much of the communications infrastructure has been decentralized. These strate
From playlist DEFCON 18-2

How To Build A Decentralized Crypto Exchange Operating On Ethereum | Session 29 | #ethereum
Don’t forget to subscribe! In this project series, we are going to build a decentralized crypto exchange, a website where we can deposit ether and tokens. You will learn how to withdraw tokens and also to develop, sell and buy orders, where we can trade the tokens for a price. A crypto e
From playlist Build A Decentralized Crypto Exchange
Lecture - 33 Basic Cryptographic Concepts Part : II
Lecture Series on Internet Technologies by Prof.I.Sengupta, Department of Computer Science & Engineering ,IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Cryptography, Security
