Steganography Tutorial - Hide Messages In Images
Steganography is the hiding of a secret message within an ordinary message and the extraction of it at its destination. Steganography takes cryptography a step further by hiding an encrypted message so that no one suspects it exists. Ideally, anyone scanning your data will fail to know it
From playlist Ethical Hacking & Penetration Testing - Complete Course
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security

FT Explainers try out their camouflage skills in a morning training
From playlist Staff Favorites

In light of the recent lock down in Brisbane, I think I'll just do this at home for exercise :)
From playlist General Fitness

Contract Law 40 III Lenawee County Board of Health v Messerly (dance ripoff)
III. SPECIAL CONTROLS ON PROMISSORY LIABILITY – FORMATION DEFENSES B. Unilateral and Mutual Mistake Lenawee County Board of Health v. Messerly (dance ripoff) To access case file, copy and paste link into browser - ianayres.com/sites/default/files/files/Lenawee%20County%20Board%20of%20Heal
From playlist American Contract Law

Imputation Strategy (Japanese Language) | Yuji Hiramatsu (Maxwell) | Kaggle Days
Kaggle Days Tokyo took place on December 11-12, 2019 at Mori Tower, Roppongi Hills, Tokyo. This was the 6th edition of our signature two-day event featuring Master and Grandmaster speakers, and a live, all-day Kaggle Competition. This edition was sponsored by Google Cloud (GCP), Data Sci
From playlist Kaggle Days | Tokyo Edition | by LogicAI + Kaggle

CERIAS Security: John Oritz: Steganography 3/6
Clip 3/6 Speaker: John Oritz · SRA International Steganography is a discipline of computer science whose aim is to conceal the existence of information. Steganography synergizes various technologies including data compression, digital signal processing, information theory, data networks,
From playlist The CERIAS Security Seminars 2008

Principles of Evolution, Ecology and Behavior (EEB 122) Sex allocation is an organism's decision on how much of its reproductive investment should be distributed to male and female functions and/or offspring. Under most conditions, the optimal ratio is 50:50, but that can change under c
From playlist Evolution, Ecology and Behavior with Stephen C. Stearns
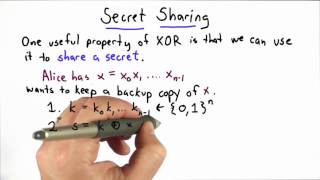
Secret Sharing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Source Boston 2010: An Uninvited Guest 4/6
Clip 4/6 Speaker: Bill Blunden, Below Gotham While there are a multitude of battle-tested forensic tools that focus on disk storage, the domain of memory analysis is still emerging. In fact, even the engineers who work at companies that sell memory-related tools have been known to admit t
From playlist SOURCE Boston 2010

Cyber Security Interview Questions Part - 3 | Operating System Interview Questions | Simplilearn
This video on cybersecurity interview questions part 3 will focus on operating systems and applications questions. Here, you will be acquainted with various questions related to operating systems, sniffing tools, Linux, and many more. 🔥Enroll for Free Cyber Security Course & Get Your Compl
From playlist Cyber Security Playlist [2023 Updated]🔥

Lec 16 | MIT 6.035 Computer Language Engineering, Fall 2005
Putting it all Together View the complete course: http://ocw.mit.edu/6-035F05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.035 Computer Language Engineering, Fall 2005

Lecture 8: Risk-Sharing Application
MIT 14.04 Intermediate Microeconomic Theory, Fall 2020 Instructor: Prof. Robert Townsend View the complete course: https://ocw.mit.edu/courses/14-04-intermediate-microeconomic-theory-fall-2020/ YouTube Playlist: https://www.youtube.com/watch?v=XSTSfCs74bg&list=PLUl4u3cNGP63wnrKge9vllow3Y2
From playlist MIT 14.04 Intermediate Microeconomic Theory, Fall 2020

Lecture 11: Contracts and Mechanism Design
MIT 14.04 Intermediate Microeconomic Theory, Fall 2020 Instructor: Prof. Robert Townsend View the complete course: https://ocw.mit.edu/courses/14-04-intermediate-microeconomic-theory-fall-2020/ YouTube Playlist: https://www.youtube.com/watch?v=XSTSfCs74bg&list=PLUl4u3cNGP63wnrKge9vllow3Y2
From playlist MIT 14.04 Intermediate Microeconomic Theory, Fall 2020

Tanner Lectures on Human Values: "The New Global Mobility Regime"
First lecture on "Borders in the Age of Networks." Achille Mbembe is a research professor in history and politics at the Wits Institute for Social and Economic Research (WiSER), University of the Witwatersrand, Johannesburg, South Africa. He holds a PhD in history from the Université de Pa
From playlist Whitney Humanities Center

Jekyll and Hyde Chapter 10 Revision
Revision for Chapter 10 - Henry Jekyll's Full Statement of the Case. Events and language analysis.
From playlist Jekyll and Hyde Revision Shorts

CERIAS Security: John Oritz: Steganography 5/6
Clip 5/6 Speaker: John Oritz · SRA International Steganography is a discipline of computer science whose aim is to conceal the existence of information. Steganography synergizes various technologies including data compression, digital signal processing, information theory, data networ
From playlist The CERIAS Security Seminars 2008