If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Networking

An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet
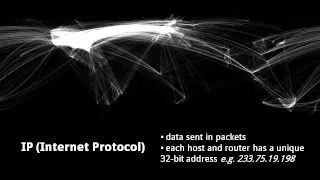
An intro to the core protocols of the Internet, including IPv4, TCP, UDP, and HTTP. Part of a larger series teaching programming. See codeschool.org
From playlist The Internet
Fundamental concepts of IPSec are discussed. Authentication Header is explained. Encapsulating Security Payload (ESP) and Internet Key Exchange (IKE) are analyzed.
From playlist Network Security

If you are interested in learning more about this topic, please visit http://www.gcflearnfree.org/ to view the entire tutorial on our website. It includes instructional text, informational graphics, examples, and even interactives for you to practice and apply what you've learned.
From playlist Communicating Effectively

This video is about the Domain Name System (DNS), a global system in which user friendly domain names are translated into IP addresses. It outlines what takes place when a client computer needs to contact a web site, including the roles of the Internet Service Provider’s recursive resolve
From playlist Computer Networks

Fundamental concepts of IPSec are discussed. Authentication Header is explained. ESP & IKE are analyzed.
From playlist Network Security
MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012 View the complete course: http://ocw.mit.edu/6-02F12 Instructor: Hari Balakrishnan This lecture covers implementation of TCP and providing reliable data transfer. The stop-and-wait and sliding window protocols are
From playlist MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012

Lec 12 | MIT 6.033 Computer System Engineering, Spring 2005
End-to-end Layer View the complete course at: http://ocw.mit.edu/6-033S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.033 Computer System Engineering, Spring 2005

🔥Computer Networks Full Course | Computer Network Security | Networking Course 2022 | Simplilearn
🔥Free Cyber Security Course With Completion Certificate: https://www.simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=CNFC07Aug22&utm_medium=DescriptionFirstFold&utm_source=youtube This video on computer network full course is designed and deployed in collaboration with re
From playlist Simplilearn Live

Why it's a bad idea to build a Virtual Private Network using TCP. Dr Steve Bagley on TCP over TCP... https://www.facebook.com/computerphile https://twitter.com/computer_phile This video was filmed and edited by Sean Riley. Computer Science at the University of Nottingham: https://b
From playlist Remote Working Technologies

Stop And Wait Protocol Explained | How Stop & Wait Protocol Works? | Computer Networks | Simplilearn
In this video on Stop and Wait Protocol Explained, we will understand the importance of applying the protocol in the networking channels. We will also look into steps involved in the working of the protocol. Topics covered in this video on Stop and Wait Protocol Explained are: 1. Introduc
From playlist Cyber Security Playlist [2023 Updated]🔥

22. Sliding window analysis, Little's law
MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012 View the complete course: http://ocw.mit.edu/6-02F12 Instructor: Hari Balakrishnan This lecture continues with an analysis of sliding window protocol and how it handles packet loss. Little's Law is introduced to re
From playlist MIT 6.02 Introduction to EECS II: Digital Communication Systems, Fall 2012

Sliding Window Protocol | Working Of Sliding Window Protocol | Networking Tutorial | Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=SlidingWindowProtocol-L6nroRENiAk&utm_medium=Descriptionff&utm_source=youtube 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybers
From playlist Cyber Security Playlist [2023 Updated]🔥

Lec 13 | MIT 6.033 Computer System Engineering, Spring 2005
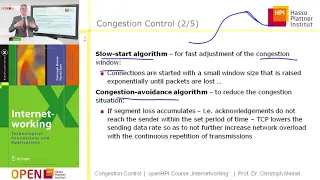
Congestion Control View the complete course at: http://ocw.mit.edu/6-033S05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.033 Computer System Engineering, Spring 2005